“Roided-out Sitting Duck” – Part Two
this mp3 audio file was automatically transcribed by Sonix with the best speech-to-text algorithms. This transcript may contain errors.
Intro:
Welcome to the Point Cybersecurity podcast. Each week, join Eric Trexler and Rachel Lyon to explore the latest in global cybersecurity news, trending topics and industry transformation initiatives impacting governments, enterprises and our way of life. Now let’s get to the point.
Rachael Lyon:
Hello, everyone, welcome to to the Point podcast, I’m Rachel Lyon here with co-host Eric Trexler. Eric.
Eric Trexler:
Rachel, this is going to be a great part two with JAG-S. The stories from last week continue. Yeah, we’re going to move to the Middle East and we’re going to talk about a little modern day story that just happened in July of twenty twenty one. It’s going to be fabulous.
Rachael Lyon:
Yeah, I’ve so many questions, too. I can’t wait. It’s been so hard to wait a week for this episode. I don’t know about you, but I have been so excited for this one to come out.
Eric Trexler:
It’s good to tease the listeners.
Rachael Lyon:
Exactly, exactly. Because how often do you wait for things anymore? Because when you do though, it’s it’s horrible and painful.
Eric Trexler:
Agreed. So anyway, with that, let’s kick off Part two with JAG-S from SentinelOne.
Rachael Lyon:
Yes, let’s do it. Absolutely. We talk to you about Kenny. You know, attackers kind of finding the rhythm or finding their way. You know, you recently wrote about this Iranian train attack, and I love that you guys called it The Meteor Express.
Juan Andres Guerrero‑Saade:
Yeah, it’s it’s the last bastion of creativity and threat intelligence. Sneak in a nice name.
Eric Trexler:
Love the naming. I just I mean, the creative naming just gets me going. It’s awesome.
Rachael Lyon:
But I love everything about this and I don’t want to steal your thunder. But you know, I love that there is kind of like this epic kind of trolling by the attacker and you know how they were directed to, you know, kind of who they were directing to call, you know, with plates or, you know, in the signage and all the things. So I please, please tell, tell our listeners more about kind of what you learned about this.
Juan Andres Guerrero‑Saade:
Ok, so this is a it’s a kind of a complicated story and a really interesting one. And I don’t know when this is going to go out, but like it continues to develop. So there are some things in there that I want to touch on that are not in the report and that it’ll probably keep evolving by the time the plays into this.
Eric Trexler:
Like, how much time do you need? We’ll record it, Rachel and I’ll be quiet, we’ll sign the NDAs.We’ll release it w hen you let us know.
Juan Andres Guerrero‑Saade:
No, let me. I’ll be as forthright as I can be, but I think, you know, this is going to keep evolving beyond today. So. We got into this thing about Meteor Express, right, then there’s a wiper attack in Iran and the sort of the railway system. And it’s particularly funny in a sense because you mentioned that this epic troll, right, they wipe all these systems, they take down the ability to coordinate these trains. And all of the displays have a picture that says, you know, trains delayed due to cyber attack. For more information, call this number. And I think it’s like six, four, four one one or something like that. And it turns out that it’s the supreme leader’s office in Iran. So I think, you know, epic troll, absolutely hilarious. Now that being said, I, you know, I try to keep the glibness in check because the other element of this is, well, somebody just deployed a wiper on critical infrastructure somewhere. So like, that’s the part where like, we’re kind of laughing and it’s Iran. So everybody finds everything acceptable when it’s, you know, when it’s Iran, North Korea, certain places, you’re like, Oh, fair game, but something, you know, I feel like in a sense, someone who is willing to do something that had it happened here, we would have been right over the Moon about right. We sorry, we would have been very, very upset about pretty pissed off. Well, I guess
Rachael Lyon:
That’s a question, too. Is it? I mean, why there, you know, is it a test? Is this like a test kind of kitchen activity or?
Juan Andres Guerrero‑Saade:
I don’t think so. So I think this is where you know, OK, let’s cover the basic ground and then we’re going to go into kind of what’s going on with this right? So there was a report out of an Iranian AV company of some of the components that they saw. And just based on some of that, I was able to rebuild the entire attack chain. You know, thankfully, we were able to find all the files and figure out what happened.
Eric Trexler:
I mean, there’s an Iranian AV company.
Juan Andres Guerrero‑Saade:
There is, I believe it’s called Padvish or something like that.
Eric Trexler:
Seriously.
Juan Andres Guerrero‑Saade:
Well, you have to think about it. Most companies can’t do business with Iran, right? If we wanted to create the EDR and make it interesting. Ok, yeah. It puts them in a particularly disadvantageous position, to be honest with you. You know, most countries, this is a the inside ball, but most countries want to develop their own navy because nobody trusts foreigners. Right. Then they try to do it and they realize it’s a monumental task. And they, yeah, they they claw back.
Eric Trexler:
And who’s buying Iranian AV software? I mean, there’s
Juan Andres Guerrero‑Saade:
An American market, either. Probably only Iran. Maybe a few other Middle Eastern partners, but
Eric Trexler:
Who thought their trains would run on time if run at all? So, I mean, Anyway, well, it’s.
Juan Andres Guerrero‑Saade:
No, no. I think you know, they’re getting.
Eric Trexler:
Yeah, she’s back to acting. Go ahead, JAGS.
Juan Andres Guerrero‑Saade:
We’ve gotten their teeth kicked in enough for the past few days. But you know, again, there’s the glib side of this. There’s the funny end of it. And then there’s a really serious one, right? Like, they’re being ravaged by COVID. They have this horrible political system that that’s showing all kinds of of terrible abuse of folks and so on. And this story actually transcends into that. So again, getting to the basics, right? We rebuild this toolkit. It’s an interesting wiper. I sort of got the detail of everything, and the wiper is called a meteor. That’s why we call it Meteor Express. I think it’s particularly important to if you discover something, get to put your stake in the ground and name it artistically. So we call it the Meteor Express, and it’s a really interesting set of activities because first of all, it doesn’t relate to any known threat actor we have seen at the time. And also it’s. Oddly clunky and poorly deployed and yet there are elements of it that are very, very well done. So to me, it’s not clear cut to say, Oh, this is a very advanced, sophisticated threat actor. It is not, but it’s definitely not somebody that just came out of the woodwork and figured out how to use a computer yesterday. Like, there’s something happening here.
Eric Trexler:
It’s probably an Israeli college classes like a final project or something.
Juan Andres Guerrero‑Saade:
Well, you know, what’s funny about that is, I think a lot of this is where we get into some of the complicated parts of threat intel, right, it’s very easy for this to get politicized, it’s very easy to kind of misstep, and I’ve written a couple of papers about this because it causes a lot of anxiety for folks, and I don’t know how many people had seen this activity before I wrote on it. But I do know of some folks that looked at it and said, Oh, this is probably Israel, and they backed off. And I personally don’t like that. I try to, you know, I’ve worked on American stuff. I’ve worked on European stuff. I’ve worked on, you know, Israeli stuff in the past. And I really don’t like the idea of just backing away from something because you think that it’s a friendly country. And in this case, I’ll be honest with you, if you asked me for my gut instinct, I don’t think it’s that. Yeah, it’s underestimating the diversity of threat actors in the Middle East to think that every semi-sophisticated attack in Israel, and to be honest with you, the quality of stuff coming out of Israel is drastically higher. It is.
Eric Trexler:
Maybe it was like a middle school class project. Well, let me put it, let me ask you a question because I saw it in the press, and I’ve only as far as I’m involved. I only know what’s in the press and probably not even half of what’s in the press, because I’m not spending a lot of time on this. But the first thought that comes to mind is. Who the hell Rachel decides to attack and the Iranian train system? I mean, who even thinks about Iran and the trains?
Rachael Lyon:
Well, that’s my question, too. I mean, that’s why I wonder is, was it a test kitchen kind of scenario, you know, where you kind of like it’s, you know, kind of low hanging fruit to go?
Eric Trexler:
It seems like an oddball target, right?
Juan Andres Guerrero‑Saade:
It absolutely is. Yeah, an oddball target, but that’s where it’s OK. So I put on my research and then checkpoint came out, and I believe it’s Itai Cohen and a couple of other folks over at Checkpoint picked up on it and wrote their own follow-up, and they found something interesting. Based on this meteor express stuff, they are able to find earlier versions of that wiper that are called stardust and comet by the attacker. And. Ok, let’s try to follow along here because it gets complicated.
Eric Trexler:
Right, I’m doing my best. I’m a podcast, but we’ll do OK.
Juan Andres Guerrero‑Saade:
I just wish we had a whiteboard right now because I think the timeline is really important. So Check Point finds these and they realize that in the code, there’s a reference to a group called Indra. And Indra is a quote-unquote hacktivism group that’s interested in attacking Syria, and they claim a couple of Syrian hacks. It’s they’re really interesting targets. It’s like a company that does money exchange services that they accuse of laundering money for the Quds Force and a private airway company that’s doing private jets for Soleimani and other folks in Iran. And so very, very interesting, very well chosen targets. And then I like to point this out because if you ask me and this is where kind of checkpoint and I stand in direct opposition, they think it’s hacktivism. I do not. We have seen a lot of examples of nation-state groups pretending to be hacktivists. The North Koreans did it. They’ve done it several times with Guardians of Peace for Sony. They used to do the WHOIS team. There are new Romanian cyber army. They’ve created a bunch of fake fronts for their activities, and so have the Russians. The Russians did Guccifer 2.0 and Poland cyber breakout cyber caliphate. Yemeni cyber army. They’ve created a bunch of these things where they make it look like it’s organic hacktivism, and in reality, it’s the same old threat actors that you can think of, and they’re using fake fronts to justify their hack and leak operations, right? Rather than saying, Look, we’re we’re the GRU providing you with stolen info, it’s well, no, we’re patriotic hackers out of Ukraine or whatever.
Speaker4:
So maybe I’m overly primed to look at it this way. But to me, this has all the markings of a fake hacktivism front. And the reason I said, you know, this is a continuum. This is a story that continues to develop and will probably develop further beyond when this podcast is revealed or released. It’s because. What Checkpoint finds to me is a specific time to limited campaign. You see a couple of attacks in Syria with this toolkit under the banner of Indra in November 20 20 in Drug Goes Dark. They stop posting on Twitter, they stop posting on Facebook and they stop using Stardust and comet the way that they were coded. Instead, we see Meteor being coded with no reference to Indra in January of 2021 and deployed in July of 2021, along with a couple of other mysterious hacks in Iran that we haven’t been able to investigate. The latest of which is Evin Prison, and I don’t know if you guys got to see the news out of this. It is really interesting and kind of terrifying, right? So a hacktivist group quote-unquote hacks Evin Prison, which is believed to be one of the darkest places on Earth. It’s basically where the Iranians take political prisoners and whatnot, and they steal tons of footage from the security cameras inside of this prison, publicly release it and then lock up and wipe the machines. And in that footage, you can even see the machines being locked up and wipe. You can watch the operators in that prison basically see this happening. And frankly, you know, I can’t make a solid assessment because I’m not doing either on those systems and I don’t have any samples. It looks like the same functionality as media or express that is not enough for anybody to make a solid assessment. I’m not going to put my hands in the fire about it, but I’ll say that it looks very similar. And the day that this hack is announced, we get a new account called EDR Ali, a new hacktivism front that claims the Evin prison hack and does the same megaton see a massive dump of stolen stuff and continues to have a social media presence and promises more attacks. Wow. So me my speculation. Is we’re seeing a group adopting fake activism fronts first for a campaign in Syria now for a campaign in Iran. And to me, that’s foreign influence. To me, that’s an established group of some sort that is basically whitewashing their exfil through seemingly, Oh, this is organic activism. People have had enough. They’ve decided to do this hacking. We would all love to believe that activism is alive and well, and maybe it is in places like Belarus, but I don’t think that that’s the situation here. That’s my honest take on it.
Eric Trexler:
So who attacks an Iranian-trained system? Right? An Iranian prison? Well, you just I’m trying to put that together like motivation, you know? Yeah, it’s the motivation disruption.
Juan Andres Guerrero‑Saade:
Let’s put it this way. Again, folks tend to immediately think about, for example, Israel in this context, but not only is Israel there, but the United Arab Emirates is there. Bahrain, Jordan, there is. Lebanon has been shown to have their own cyber espionage capabilities. There are quite a few well-resourced groups and in particular, I mean, we’ve been seeing a lot come out about the Emirati cyber program between stuff with dark matter and everything that happened post Cyber Point contract and the amazing stories of Chris being put out on Reuters about karma and how former NSA contractors had basically been helping them build capabilities in the Emirates. I’m not pointing at them in particular, but I’m saying we’re oversimplifying the Middle East. If we think that it’s really one one attacker and a one victim in either direction. I mean, the Iranians have been pissing plenty of people off with their own wiper attacks for years now, including the South. But who
Eric Trexler:
Do you? Who do you hurt if you hack the prison and the train system?
Juan Andres Guerrero‑Saade:
Well, I think in a sense, you in a sense what you are doing is chipping away at the legitimacy of that government. It’s not that you are really going to disable them, it’s that you’re essentially showing this general uncoordinated weakness that comes along with being unable to stand up to some ephemeral force. Worse yet, when you can claim that it’s locals right, the idea that your own people are against what you’re doing is part of the propaganda force that comes along with the hacktivist group.
Eric Trexler:
So then if you take the train system, which a lot of people use. Right. I’m assuming the administration, the people running the company of private cars and planes and helicopters and things, but the people are on the train system. They use six four four six four four one one. The phone number, I guess, for the supreme leader’s office. Right. So I understand that in the prison showing what’s going on in this very dark place, maybe you start to pull it together. I guess you’re right. I mean, your question does make them look bad.
Juan Andres Guerrero‑Saade:
You’re putting into question the legitimacy of it. I think it’s important in a sense, because it’s a lot easier to deny obscure hacks that happen inside of, you know, the ministry. Apparently, they also hack the Ministry of Urban Development and Roads or something. Yes. Yes. You know, it’s like, I mean, who knows, right? They can just say nothing happened. And the Iranians often do they either that government will either come out and say, Oh my God, we are being pummeled by cyber attacks, and it turns out to be nothing. Or they’ll say nothing happened here. And it turns out that a whole ministry got taken down. So in a way, targeting something that normal everyday people rely on is a fantastic way of just showing egg in their face, right?
Eric Trexler:
This is not powerlessness. The powerlessness of leadership. Right, right, right.
Juan Andres Guerrero‑Saade:
It’s something that you began with with Stuxnet. I mean, we’re talking about part of the and I hate to invoke the ghost of Stuxnet because it’s brought up in every conversation. But part of the power of Stuxnet was psychological. Once the Kim Zetter wrote such a fantastic book on this, if folks haven’t read it. Countdown to zero days. Probably the best threat Intel story out there. Kim Zetter Fantastic journalist for this, but part of the effect of Stuxnet was they were doubting their own competence. They were firing scientists. They were chasing their own tails, replacing equipment. It’s a psychological effect to say, Oh God, we just can’t get our act together to get this done. And now we’ve got something similar. You know, we’re experiencing it in the U.S., too, right? The ransomware epidemic for enterprises is definitely making us look like this horrible. I think I use the expression royd it out sitting duck, right? Like we were the most powerful cyber nation on Earth. But we’re also just getting slammed all day and we can’t do anything about it. And you know, the show situation in Iran.
Rachael Lyon:
I know that’s what I laying down..
Eric Trexler:
Sitting duck with Jags. But you’re right. I mean, they’re incredibly vulnerable, easy targets, and we can’t do a lot about them.
Juan Andres Guerrero‑Saade:
It’s I mean, it’s a sad situation to have what is arguably the most power in cyberspace and to have your hands the most tied out of anybody else, right? The U.S. is
Eric Trexler:
The most vulnerable too
Juan Andres Guerrero‑Saade:
Yeah, we’re all that all comes down to dependency on technology, right? It’s such an enabler. It’s such a source of our power. And we have the largest corporations economically, the largest corporations on the planet. They’re all technology companies, right? And that shows the great promise of America is largely built on the tech sector right now. So if if you can chip away at our ability to depend on that, you know, I think that’s part of the ridiculousness of the arguments that we have about cyber war and particular cyber on cyber, right? It’s like, Oh, if we get hit, then we’re going to retaliate with cyber. It’s like if you take down some systems in Russia or in Iran or in China, I mean, the trains aren’t working. We’ll walk like there’s fine. If you do that in the U.S., like look at what happened with Colonial. They didn’t even hit the OT system. They just took down the billing and I had to pay like seventy five dollars to fill up my tank here in Miami, even though that pipeline doesn’t even reach here. But what about the people who
Eric Trexler:
Are putting gasoline into into plastic bags?
Juan Andres Guerrero‑Saade:
Oh yeah.
Speaker3:
So to show some problems,
Juan Andres Guerrero‑Saade:
Our collective wisdom is not what it what we’d like it to be.
Eric Trexler:
That could be a different show title.
Rachael Lyon:
Yeah, we had someone there was someone in Texas that had filled a trash trash can in the back of a pickup truck, and there wasn’t even a top on it. So I’m like, How do you how do you drive it?
Juan Andres Guerrero‑Saade:
Well, you’re just getting high on the way out on figuring out how you one
Eric Trexler:
Spark, though you’re you’re you’re your firework.
Juan Andres Guerrero‑Saade:
I don’t know what to tell you.
Eric Trexler:
Yeah, we’re not going to fix that one today. So. So Jags, I think we’re going to turn this into a two parter. The stories are awesome.
Rachael Lyon:
Absolutely.
Eric Trexler:
How did you get? How did you get into this career path? Like you say, this is where I want to go.
Juan Andres Guerrero‑Saade:
So my career path is super unlikely and I’m incredibly fortunate to have ended up where I did. I was a. Philosophy major, and that was my whole thing, I was just going to kind of stick to really obscure German philosophy that nobody ever wants to read. And somehow that that turned into a lot of intelligence analysis work, which I really enjoyed and eventually being on the receiving end of a lot of cyber attacks and know having no local expertise, you know, develops into a fascination for something that was not immediate to my skill set, but that was interesting enough to be worth the dedication and devotion to try to learn and learn and learn. And I credit my time at Kaspersky a great deal. I had the pleasure of working in global research and analysis team for four or some years, with amazing researchers like Coson Ryu and Kurt Baumgartner and Brian Bartholomew, and all these fantastic folks who took the time to teach a lowly analyst how to do things. And it’s just been getting into trouble ever since, right? Like I mentioned, I I don’t. I lack the common sense, or at least the survival instinct to not look at certain things. And it has led me down some really interesting roads
Eric Trexler:
That but you’re not you’re not getting a job as an obscure German philosopher at Kaspersky on that right? I mean, like, where are you working? Where you determine like that path? Because we have a we have a tremendous amount of need for people like you. Yeah, not not Rachel. And I was like, How do you get started? Because we get a lot of people want to know. How do I get into the business, yes, like, what’s that journey?
Juan Andres Guerrero‑Saade:
So I think my journey isn’t necessarily the one that I would immediately prescribe for others, but I would say I am definitely not an outlier in the thread intel research space in the sense that there’s a lot of folks that I know a lot of folks have never graduated high school. They got their GED and they just, you know, went into this because it’s what they loved. And I know people that are PhDs in physics and just people that are just all over the spectrum who just love puzzles and love doing this kind of research. And I think that should be encouraging, particularly to folks who have a mind for critical thinking, who have a mind for everything that would make you a good intelligence analyst or somebody who’s into international relations and geopolitics to say, Look. Just because you don’t have the technical information right now doesn’t mean you are barred from the space. I’ve gone on the record and I did this at a Carnegie Mellon lecture, which was probably not the nicest thing to do for a tech, a purely technical department. But I’ve gone on the record to say that I would rather hire a really smart international relations or intel analyst and teach them the technical stuff the way it was taught to me. Rather than take a course grad and try to get them to think more broadly and try to understand motivations and and cui bono and international relations and what happens between Iran and the Emirates and so on. It’s so much harder to broaden a technical person’s thinking than it is to take a broad minded individual and teach them technical things.
Eric Trexler:
It reminds me we had George Randall on, I don’t know, a year or two year and a half two years ago. Probably he’s from an air talent acquisition perspective, and he wrote a book on. The talent weren’t he talks about one of the major themes is higher for characteristics, train for skill, don’t hire for skill, right? And one of the stories they use in the book is Navy SEAL Story. Like every Navy seal, who’s a Navy seal already went through buds, the Navy SEAL training program. You can’t get non Navy SEALs with Buds qualification, so you’ve got to look for the characteristics you can’t say looking for a navy seal to be a navy seal because they already are.
Juan Andres Guerrero‑Saade:
Right, right.
Juan Andres Guerrero‑Saade:
You’ve got to look for the people like you out there that have those characteristics. So when you say you’re an obscure German philosopher, like, that’s what you like, that was your interest. Yeah, to me, having having actually worked with and, you know, I was managing, overseeing, I guess, a malware, an advanced malware lab capability. They were all over the place. I mean, we provided Xboxes, Nerf guns, you know, crazy wacky lunches. But but the the spread of a variety of the people in the lab who you’re working with Marco Figueroa right now, I mean, Marco is not normal, let’s be honest, right? But he’s he’s amazingly capable and brilliant, right? You’ve got to look for people who have characteristics. Yeah, we’re going to put a job ad out for looking for obscure German philosopher.
Juan Andres Guerrero‑Saade:
Right? Like, it doesn’t work. Do not do that.
Eric Trexler:
So that’s why I ask about your journey, because I think it’s I think it’s something that there are a lot of people across the globe who would be really good. Yes, at this business,
Juan Andres Guerrero‑Saade:
I think so. There’s a couple of things here. One of them is it’s a shame that we don’t have a good talent pipeline. I think a lot of universities are kind of failing to put this together. And it’s just it’s a shame that we don’t have a way to really churn out talent because we need it. I mean, I am not worried about job security. Nobody in this space should be worried about job security. We have enough work for ten times the amount of people that we have here, so please bring them along, right? The issue is right now we’re kind of living in the apprenticeship model. You’re if you’re lucky enough to go somewhere with great folks, then you learn from them how to do things. And then someday you, you pay it forward and you teach somebody else how to do things. And that’s tough. But the corollary for me is look at something like Bellingcat, like Bellingcat is fantastic. It’s brilliant. It’s I’m not
Eric Trexler:
Familiar with Bellingcat. Forgive me.
Juan Andres Guerrero‑Saade:
Oh my god, you’re missing. You’re missing out, you’re missing out.
Eric Trexler:
So you educate me. That’s why we do the show.
Juan Andres Guerrero‑Saade:
Bellingcat is a UK collective of citizen journalists. Ok? Basically, people who really like are passionate about some obscure subject and decide to use open source intelligence to figure out what the hell’s going on. They’ve done a really notable work, for example, investigating the downing of MH 17, the poisoning of the Skripals and the U.K. they’ve done a lot of very significant work. They’re also helping to track, you know, human trafficking victims like anything that they can basically take some leads of information and use open source intelligence to just figure out what’s really going on, identifying videos of victims in Africa. You know, what country is this? Who did this? You know, it’s fantastic because honestly, there isn’t a there really isn’t any gatekeeping about who can be a part of this effort. It’s very easy for folks to come in and say, You know what, I just really care about this. I’m going to learn the tools and techniques, and I’m going to contribute and other folks are going to check my work. And if it’s worthwhile, we’re going to publish it. And I think there should be a similar mentality when it comes to threat intel and infosec, which is to say, Look. Start your blog, start your journey. Tell us what you’re working on. Show us what you’re learning. And it’s I think, yeah, you’re not going to put out a job requirement for someone who’s into obscure German philosophy. But I think it’s much easier to extend the hand to somebody who has a blog and you’re like, Wow, like, I mean, they don’t know everything, but you know this this person, they’re a student or whatever, or they’re just a random individual who really cares about this, like they’re on to something. Let’s hope so. I think that’s an easier way to get a foot in the door to show your curiosity and show what you can do on your own. And good hiring managers should be able to say if they can do this on their own. Imagine what they’ll do with our tools and our mentors, right?
Eric Trexler:
And when we’re mentoring them and working with them. So one of the pieces of advice then is get creative, get out there. But also when you look for that first or second job, find a good mentor, find somebody who can teach you because it is an apprenticeship model. I would argue with that. The only difference I would say is you can look at things like maybe DHS, but definitely NSA, Cyber Command, CIA in the States, GCHQ in the UK. You know, I’m sure the Iranians have a have a good training program to over there and the offensive work. Does in my experience, anyway, it does make good defensive people like that’s probably the most structured training program. You’re not going to go to a college necessary and B and figure this stuff out overnight. But if you’re doing the offensive stuff, you get to think like the adversary and then can defend somewhat against them.
Juan Andres Guerrero‑Saade:
Yeah, I think that’s an interesting argument for folks to consider going the government route. I mean, obviously great to be able to serve your country. And to be honest, even though you’re going to be underpaid, you are going to get opportunities to do things. You’re never going to be able to do anywhere else, right? I can’t I can’t hire you and say, Hey, go pop those command and control servers. Let me know what you find. So there’s some there’s definitely something to be said for that. I think from the industry we can. I think we have to admit that, for example, Unit Eighty two hundred has figured out how to churn out amazing talent they are on to. Something is real, Rachel. Yeah. I mean, there the rest of us are not on to. I mean, they just churn out a massive amount of great people. We should probably ask them how to set up a talent pipeline and
Eric Trexler:
Look at the flourishing cybersecurity industry in Israel. I believe yes, much due in part to the work that’s done over there.
Juan Andres Guerrero‑Saade:
Mm hmm. So I mean, there’s something to be said for there is a way to do this. I think we’re being, you know, maybe we’re being failed by the rigidity of the academic space not to set up better programs for it. But in any case, this is also a space where knowledge isn’t obscure. You can find most of the great tutorials for learning how to reverse and debug are freely available online. Back from the late nineties, early two thousands when people were just trying to crack software because they lived in Eastern Europe and they couldn’t buy it. Most of the stuff you need is freely available. No starch press does sales on their books basically every month. And if you are a starving artist and you really can’t pick that up, you could probably steal them online. Forgive me, Bill Pollock, but I’m saying you can get your start. You can do it. It’s it’s more about dedication, and I think that’s something that we really shouldn’t underestimate, even for people that already have their foot in the door. If you are purely an intel analyst, find the time to learn the technical side of the house. The more that you need to depend on other people for your technical end, the more you’re missing parts of the picture. So not to not to preach against Work-Life Balance or whatever, but this is your passion. There’s a lot of room to grow.
Rachael Lyon:
Absolutely.
Eric Trexler:
Great advice and even reach out to famous published researchers. I’m betting nine times out of 10 they’re going to if somebody reaches out and says, Hey, I have a question about the industry, I’m betting people answer.
Juan Andres Guerrero‑Saade:
Yeah, absolutely. I mean, there’s a reason why, you know, DMs are open for a lot of folks, and Twitter has given everyone a voice for better or worse. And you can you can reach out to amazing individuals and half the time they’ll answer. So yeah, might as well try.
Eric Trexler:
And fascinating, Rachel.
Rachael Lyon:
I know
Eric Trexler:
Know to end the week.
Rachael Lyon:
Stunned silence.
Eric Trexler:
That you didn’t have this on the set with all my children.
Rachael Lyon:
No, no, it was quite different.
Speaker4:
It was given her such a hard time about her.
Eric Trexler:
Oh my god, I love it. I’m so are you kidding, Jags? I am so impressed.
Juan Andres Guerrero‑Saade:
It’s a diversity of skills. It’s a wide range of skills.
Rachael Lyon:
Exactly, exactly. And cyber takes all comers. I love that
Eric Trexler:
Rachel is amazing at what she does. So a couple of years ago, we were at RSA and we did a show. Rachel was going to listen in one of the podcasts and. We surprise her, I was with our CTO at the time we were doing a show about RSA, and Rachel was the featured guest she was supposed to listen in. She had no prep or anything. We’re huddle around a little Blue Yeti mic in a room right off of Moscone Center. Yes, and we put Rachel on the spot and she was freaking amazing. I don’t know the podcast episode. Yeah, but I believe, yeah, if you’re in marketing, if you’re in PR and you’re running shows and things, go listen to it because she talks about what it takes to put the show on what’s right? Anyway, she was a pro day one. I mean, I mean, she had no idea she came in live about, I don’t know, Rachel, 30 seconds into the show, we announce you as the featured guest and she just rolled with it, and that’s her acting experience. She’s a pro.
Rachael Lyon:
Well, it helps when you have good people to talk to. Like today. I mean, it’s, you know, fascinating people with all these amazing stories. I mean, it makes it really easy to have a really good conversation.
Juan Andres Guerrero‑Saade:
Thank you. Thank you for the opportunity. I mean, honestly, I don’t get to nerd out about these things often enough. You know, you’re running looking at the next case, but there are so many great stories in this space and
Eric Trexler:
There are great stories that we can’t wait to hear. What do you think is next? Are you working on anything next?
Juan Andres Guerrero‑Saade:
Oh, all kinds of things. So I mean, we try to. There is a bit of a competitive streak and we all kind of try to impress each other and come out with new things. So I’m actually
Eric Trexler:
Challenge out there now, lay the gauntlet down for everybody in the business.
Juan Andres Guerrero‑Saade:
Well, so I’m working on some, some special techniques to analyze go malware. There’s there’s some, really. I like to do something that we’ve nicknamed cyber paleontology like. I like to look back at stuff we tend to. The industry tends to be very now focused, you know, Monster of the week. Oh my God, SolarWinds, oh my God, say, oh my like every week is a different thing. And the truth is that we don’t have the resources to ever fully analyze any of these incidents. So I like to, you know me and review a few other folks really like to take old incidents and say, Well, what? What can we understand now, right in the vein of Moonlight Maze? What do we understand now? So I’m working on a really old school operation now, and honestly, I’m just waiting for the in-person conferences to really come back so that I can have a good venue to be like, All right, like, this is this thing I’m working on now.
Eric Trexler:
You’re hitting my area of expertise. Guess what? They’re shutting down. We just had another government shut conference shut down today. I don’t think you’re going to be back in person until probably second half of twenty two at this point.
Rachael Lyon:
January, January, January,
Eric Trexler:
Maybe April. I’m betting I put a dollar down. No, no January. But I don’t. I don’t want to bust your bubble. I just want to be honest with you. We’re seeing them cancel.
Juan Andres Guerrero‑Saade:
I’m selling myself the dream just because, you know my inner attention whore, you know? Yeah, they can’t take it. I need to get on stage and show
Eric Trexler:
I’ll come back on the podcast.
Juan Andres Guerrero‑Saade:
I love to do it. Yeah, please.
Rachael Lyon:
Yeah, we’d love to have you. It’s amazing.
Juan Andres Guerrero‑Saade:
We’ll have a lot more stories to cover.
Eric Trexler:
Ok. Well, Rachel, it’s Friday evening this time we’re recording, is that a wrap?
Rachael Lyon:
I think that’s a wrap. Yes.
Eric Trexler:
Take us home.
Rachael Lyon:
All right. Well, everyone, thanks again for joining us for this week’s podcast with Juan Andres Guerrero Sodhi. Well, there you go. Close. Yes, that’s perfect. Better known as Jag’s, but what an amazing conversation. Thank you so, so much for joining us today. We can’t thank you enough.
Juan Andres Guerrero‑Saade:
Thank you both. This is fantastic. I appreciate it.
Eric Trexler:
This was outstanding.
Rachael Lyon:
Yes, I hate. I don’t even want to ruin it. But you have to put the plug in, smash the subscription button, get a fresh episode every single week in your email. And it’s like Eric and I are just, you know, showing up at your doorstep and and having a nice conversation. How lovely is that? So for that laugh? So until next time, everyone stay safe.
Intro:
Thanks for joining us on the To the Point cybersecurity podcast brought to you by Force Point. For more information and show notes from today’s episode, please visit W four point Gov podcast. And don’t forget to subscribe and leave a review on Apple Podcasts or Google Podcasts.









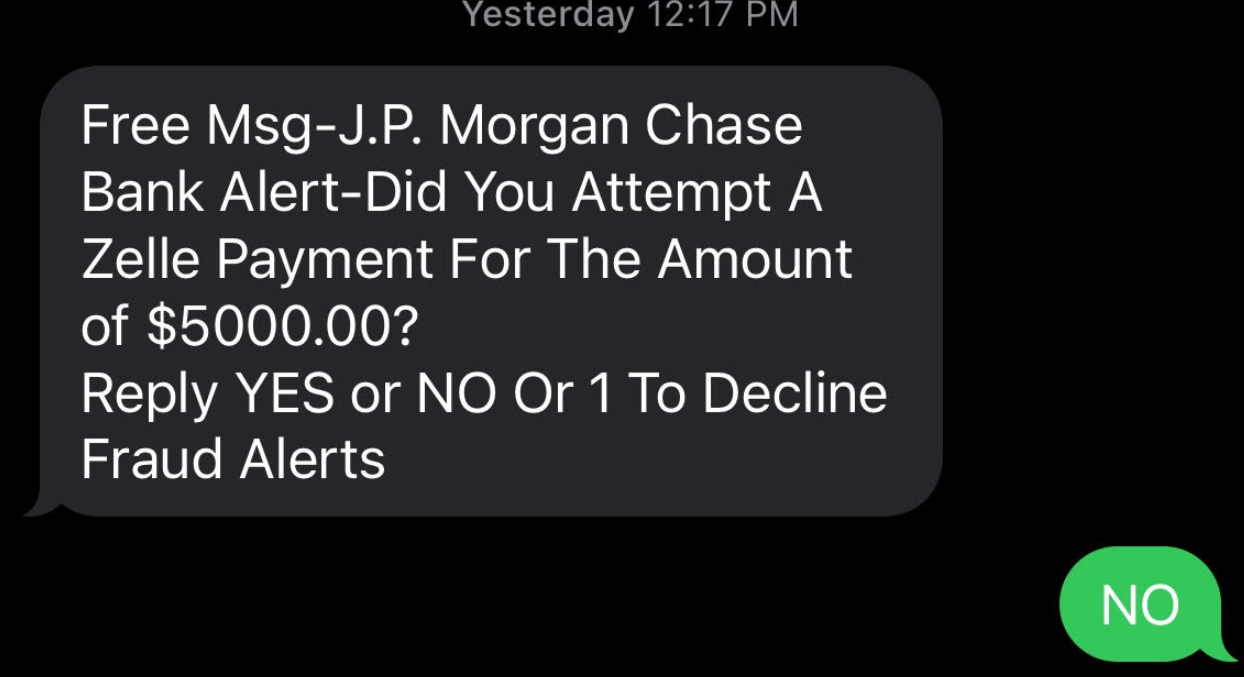








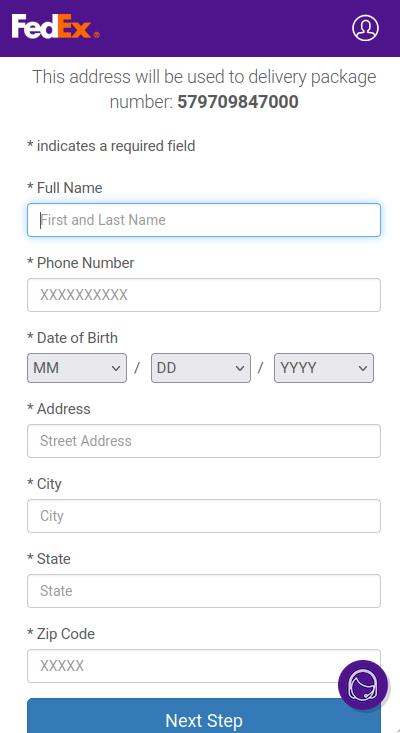 While every fiber of my being hopes that most people would freak out at this page and go away, scams like these would hardly exist if they didn’t work at least some of the time.
While every fiber of my being hopes that most people would freak out at this page and go away, scams like these would hardly exist if they didn’t work at least some of the time.