Power for the People | Cyber Threats in the Energy Sector and How To Defend Against Them
Powering the infrastructures that sustain how people communicate, work, and live, our dependence on the energy sector has pushed it to the top of the list of targets for cybercriminals. Concerns on how to defend this critical sector have only been magnified by ongoing dilemmas in the economic and political landscapes.
Beyond the immediate financial losses and operational disruptions, attacks on a critical sector like energy have cascading effects on other sectors, such as manufacturing, healthcare, and transportation.
This blog post outlines these effects and challenges, exploring the reasons behind growing cyberattacks on energy grids and what energy and utilities suppliers can do to safeguard themselves from advanced threat actors.

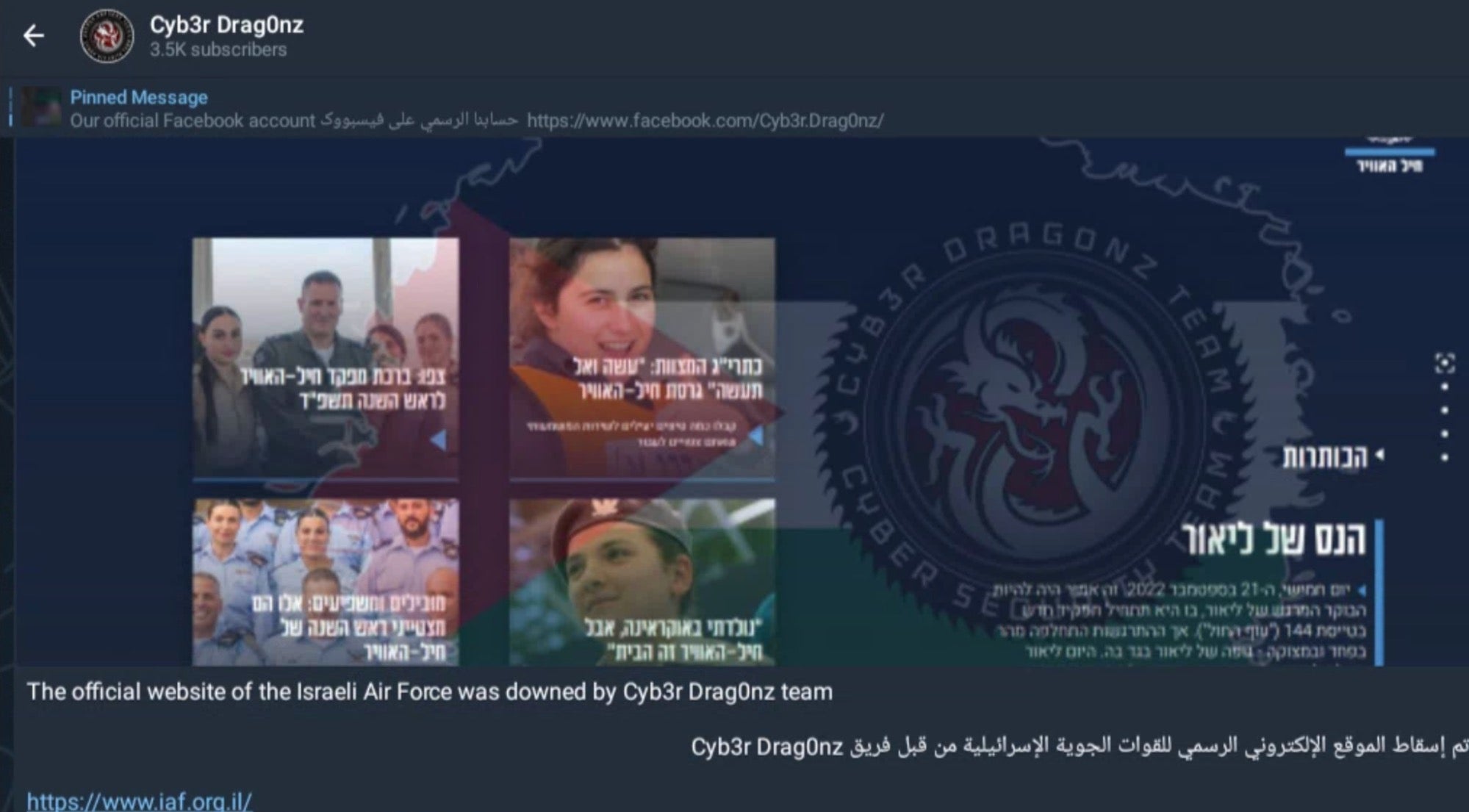
A Global Snapshot of Recent Attacks on Energy
Some of the most notable attacks on energy and utilities providers have occurred in the past few years alone, marking threat actors’ increasingly steep interest in this sector.
Ransomware Extremes | How the Colonial Pipeline Attack Spurred Changes to US Cybersecurity Policies
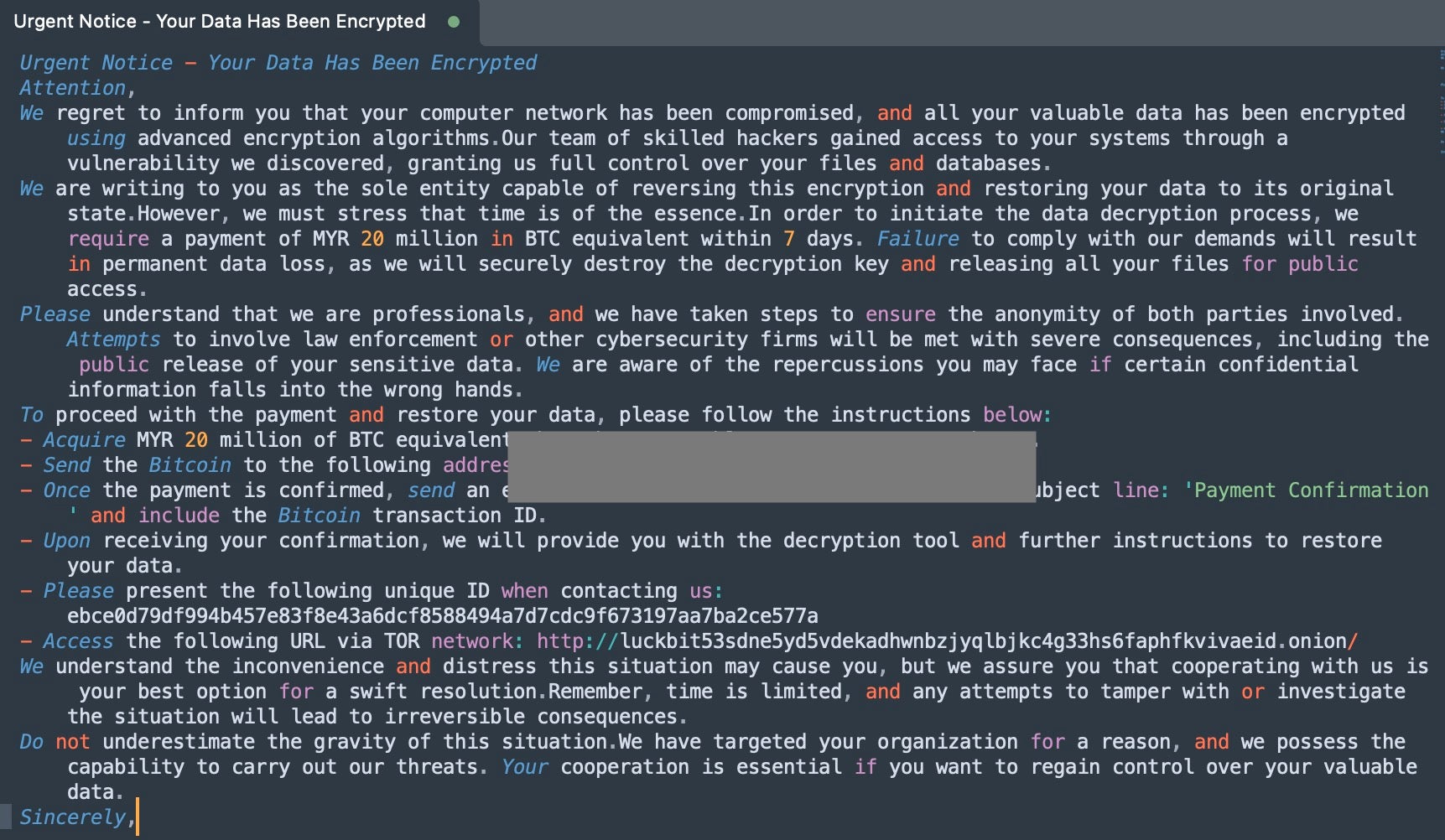
Early in the morning of May 7, 2021, a ransom note was uncovered by a Colonial Pipeline employee, revealing a successful systems breach attributed to the DarkSide ransomware group. DarkSide had managed to exploit an outdated virtual private network (VPN) account, the first step leading to one of the most significant cyberattacks on the energy infrastructure in US history.
DarkSide threat actors had encrypted an estimated 100 GB of sensitive, business-critical data within Colonial’s expansive operational technology (OT) network. In response, Colonial Pipeline suspended all operations, including the delivery of over 2.5 million barrels of refined gasoline a day to U.S. customers. Affecting businesses and millions of individuals along the East Coast of the United States, the fallout included lengthy gas lines reminiscent of the 1970s, price hikes, panic buying, and the closure of numerous fuel stations.
Shortly after this attack, the Transportation Security Administration (TSA) released a directive mandating that pipeline operators promptly notify CISA of all potential cyberattacks. The directive also required the presence of an on-site cybersecurity coordinator. A second directive soon followed, directing pipeline operators to address vulnerabilities, enhance their defenses, and create contingency plans for future security events. Earlier in 2023, CISA unveiled a Ransomware Vulnerability Warning Pilot (RVWP) program, set to support critical infrastructure providers with the best practices and tools needed to protect against ransomware attacks.
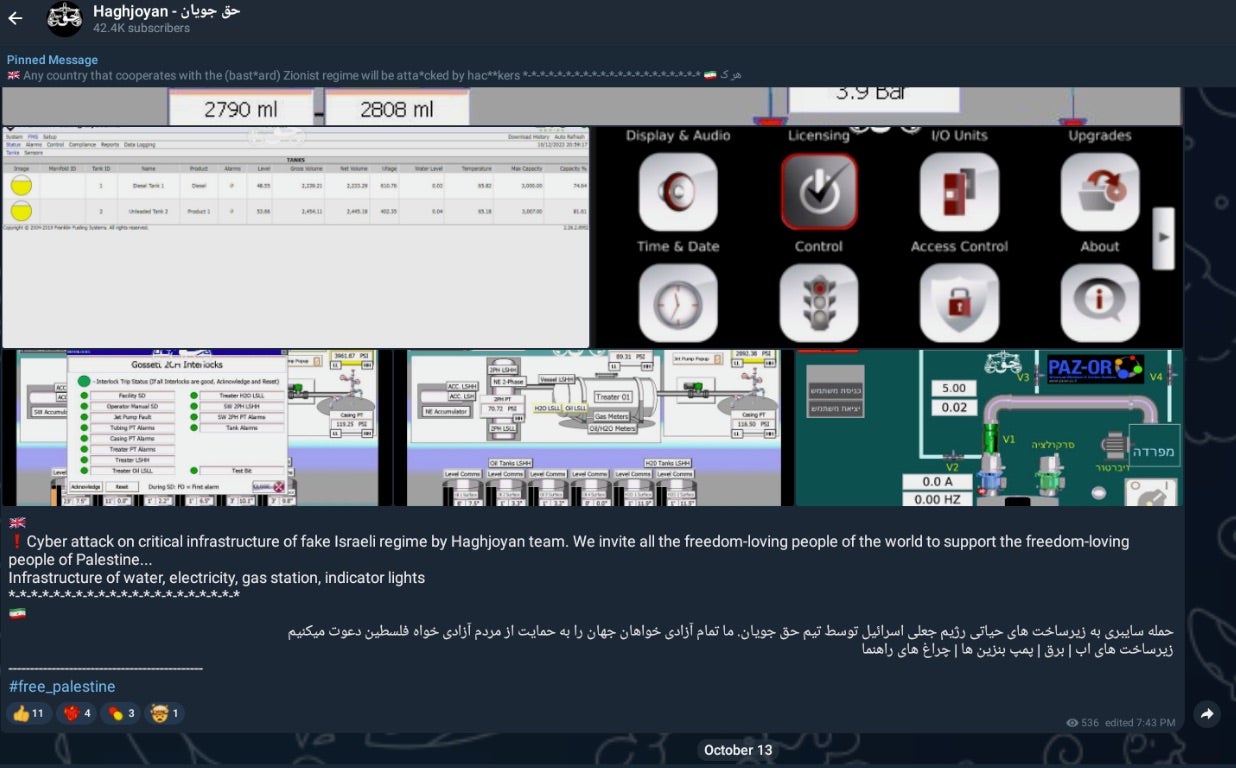
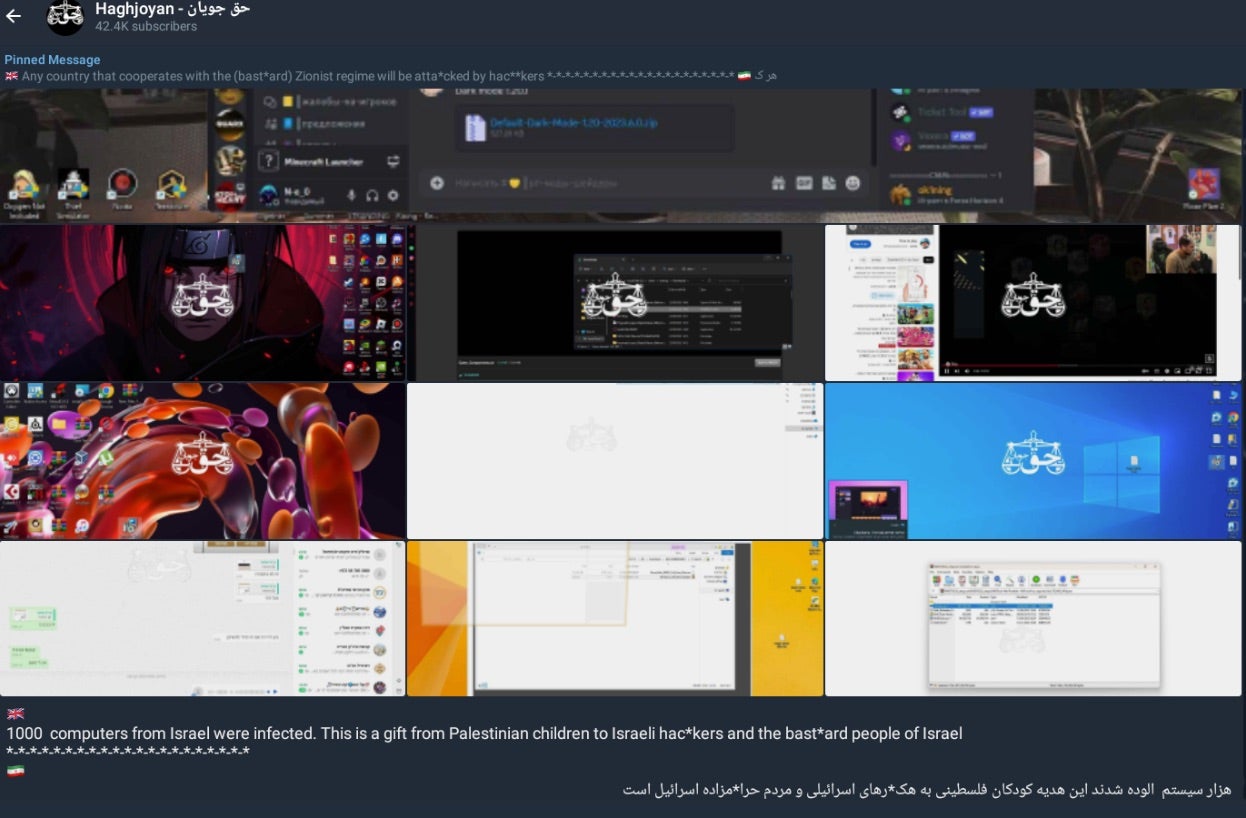
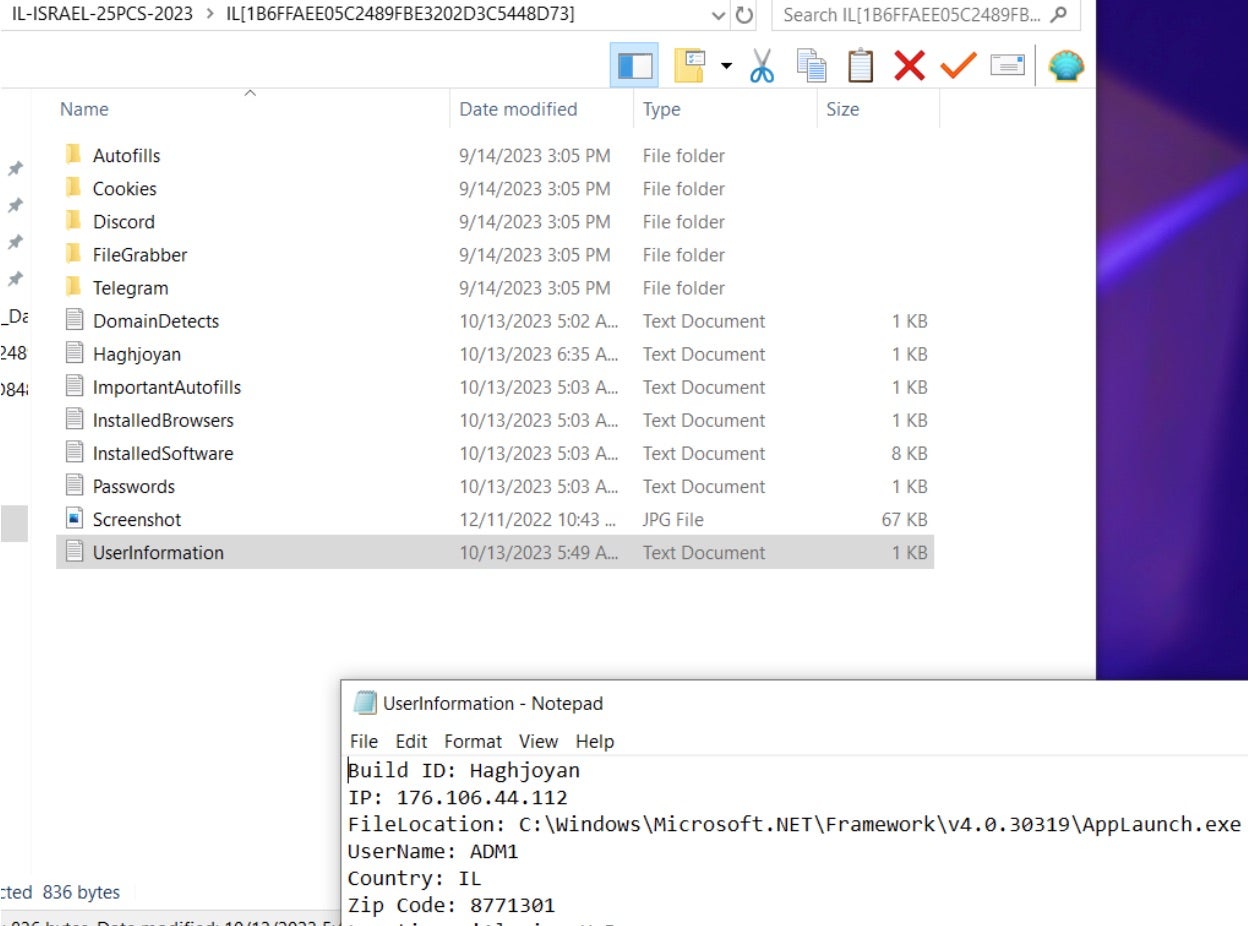
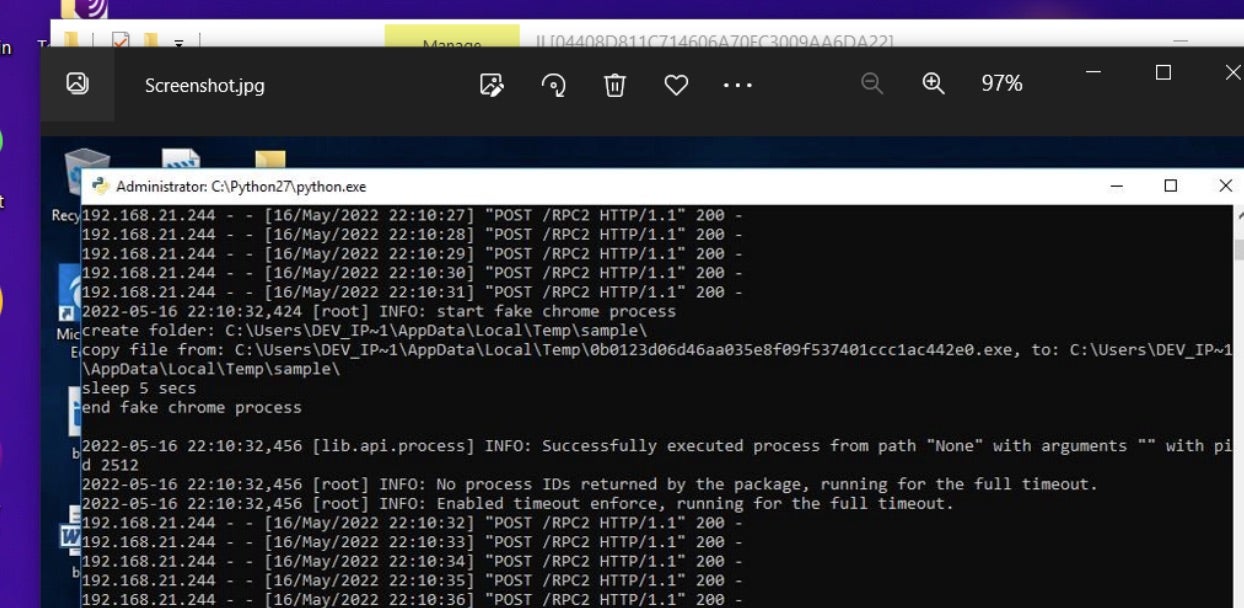
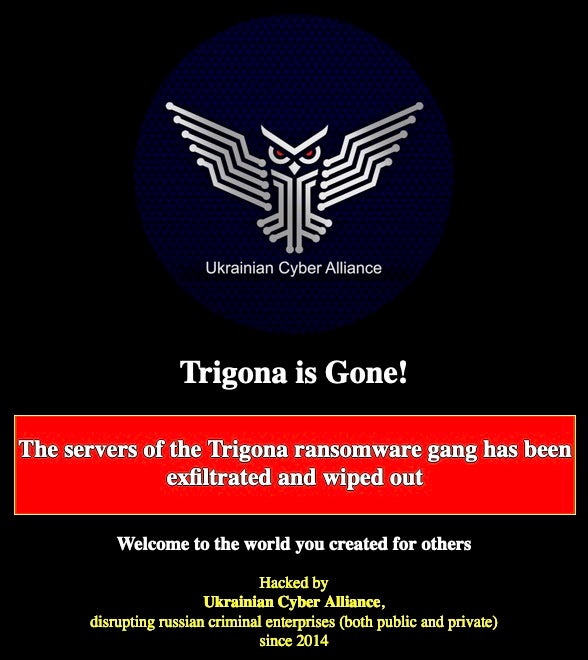
New Battlegrounds | Russian-Based Attacks on Energy Providers
At the onset of the invasion of Ukraine in early 2022, Ukrainian government officials revealed that Russian state-sponsored threat actors aimed to compromise the Ukrainian power grid, intending to trigger a blackout that would have impacted a staggering 2 million people. The attack involved the use of a wiper – a specialized form of malware designed to take down targeted systems by erasing critical data. Had the hack been successful, it would have caused the world’s biggest cyber-induced blackout to date.
One month after the invasion of Ukraine, President Biden issued a statement discussing the heightened potential of Russian cyberattacks against the US energy infrastructure in retaliation for imposing economic sanctions. Several US energy companies and more than a dozen others in associated sectors all reported to have experienced abnormal scanning from Russian-linked IP addresses, likely indicative of early reconnaissance in which threat actors scan targeted networks for vulnerabilities that could be used in a future attack.
Threat Actors’ Eyes on Energy | Why the Sector Is At Risk
The energy sector powers the reliability of all other sectors, making it the linchpin of all critical infrastructure. Extending far beyond single power plants, pipelines, or grid systems, the attack surface for the energy sector exists at every point on the power chain. This dependency on interconnected networks and industrial control systems (ICS) creates vulnerabilities that malicious actors find extremely attractive. Cyberattacks on the energy sector can disrupt the flow of essential resources, leading to power outages, fuel shortages, and economic instability.
Several factors underpin the risk faced by the energy sector.
Evolving Digitalization & Interconnectivity
Rapid digital transformation within the energy and utilities sector has expanded its attack surface. Increasing connectivity, cloud adoption, and the internet of things (IoT) integrations have introduced many more entry points for threat actors. This digital evolution, while boosting efficiency and monitoring capabilities, has also introduced vulnerabilities that malicious actors can exploit. Modern technologies have accelerated digitalization but also make this sector more susceptible to cyber threats than ever before.
Adding another layer of intricacy is the interdependence of all essential parts. For instance, a power outage in one region can have large ripple effects, affecting electricity availability in other parts of the country as smaller grids have to adapt to meet the sudden demand. Similarly, a compromised oil pipeline not only causes localized shortages but can trigger nationwide spikes in gas prices, highlighting the intricate web of interconnections within the industry.
Dispersed Geographic Locations & Reliance on Third-Parties
Energy and utility providers face an expanding attack surface, stemming from the challenge of securing geographically scattered assets such as hydroelectric dams and coal-fired generation plants. Safeguarding against multiple threats in a dispersed environment presents security leaders with a logistical challenge.
Making this more complex is the energy sector’s reliance on third-party supply chain relationships. The industry, which encompasses a blend of private and public ownership, is built on strategic partnerships among the various stakeholders. As a result, securing all the various components that make up the energy industry requires collective action and responsibility among diverse agencies and organizations, each of which have their own cybersecurity challenges.
Economic Incentives for Attackers
The energy and utilities sector is an enticing target for financially motivated cybercriminals. Ransomware attacks, in particular, have become increasingly prevalent, with actors seeking hefty payouts to unlock critical systems. Colonial Pipeline’s CEO explained that the company paid the “highly controversial” $4.4 million dollar ransom given the essential nature of the company’s infrastructure. The strains of recent times, including post-Covid economic uncertainty, inflation, and job losses, have created fertile ground for cyber extortion schemes, exacerbating the risk faced by this sector.
Gaps Between Physical & Cyber Infrastructure
Operational technology (OT) systems control and monitor physical processes, such as power generation, distribution, and transmission. These systems are increasingly interconnected with information technology (IT) networks to improve efficiency, optimize operations, and enable remote monitoring and control. This connection creates a bridge between the physical and cyber infractures, allowing data and commands to flow between them. However, gaps between the two greatly increase cyber risk.
The interdependencies between physical and cyber infrastructure mean that issues on the IT side have real-world consequences. For instance, a cyberattack on a power plant’s IT network can potentially disrupt the OT systems responsible for controlling critical processes. Conversely, physical events, such as equipment failures or power outages, can affect the availability and security of IT networks.
Powering Up Cyber Resilience Within the Energy Sector
The challenge for those in this sector lies in staying ahead of ever-evolving threat tactics. The following guidelines can help energy providers to mitigate risk and build a stronger, proactive cybersecurity posture.
Manage Cyber Risk Within the Supply Chain
Managing risk in the energy supply chain starts with understanding all current vendor relationships, including OSS dependencies, and creating stricter standards for procurement. Start by reviewing supplier assessments for all in-use vendors and agree on procurement processes and shared security responsibilities. To integrate cybersecurity into the procurement process, mandate software bill of materials (BOMs) to track all digital components in a system across the supply chain to identify potential issues.
Implement Hardware Authentication
Hardware authentication offers a robust approach to user authentication – a critical element in securing geographically dispersed OT networks in the energy sector. This strategy hinges on the use of a dedicated physical device, typically a token or hardware key, alongside a primary password. This dual-factor authentication method enhances access control by requiring both something the user knows (the password) and something the user has (the physical token) for access. Hardware authentication serves as a strong defense against unauthorized access, ensuring that only authorized personnel with the right physical device can interact with sensitive systems.
Leverage User-Behavior Analytics (UBA)
Going beyond predefined patterns or signatures, user-behavior analytics (UBA) delves into the nuanced behaviors of users within a given system. UBA’s strength lies in its capacity to alert on unusual or suspicious activities based on a comprehensive understanding of typical user interactions with a particular environment. By creating behavioral baselines for legitimate users, UBA can swiftly flag any deviations and pinpoint potential security breaches or insider threats.
UBA works by harnessing machine learning (ML) techniques to decipher the underlying intent behind user actions. This continuous learning and adaptation enable UBA to evolve alongside the ever-changing threat landscape, enhancing its accuracy in recognizing even the most subtle anomalies in user behavior.
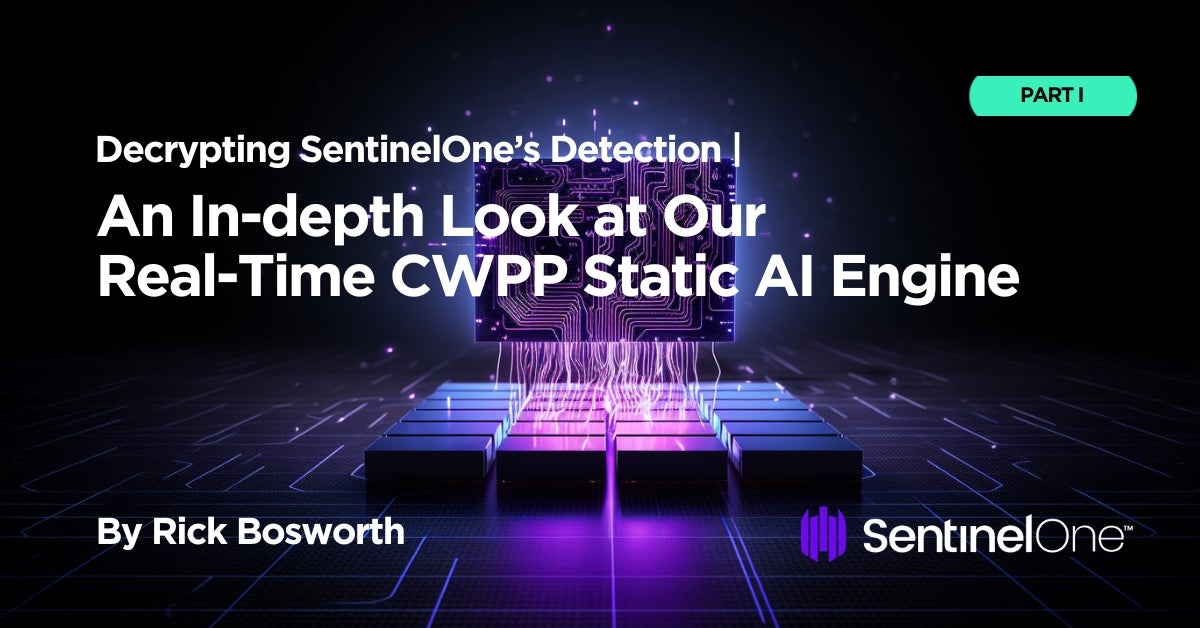
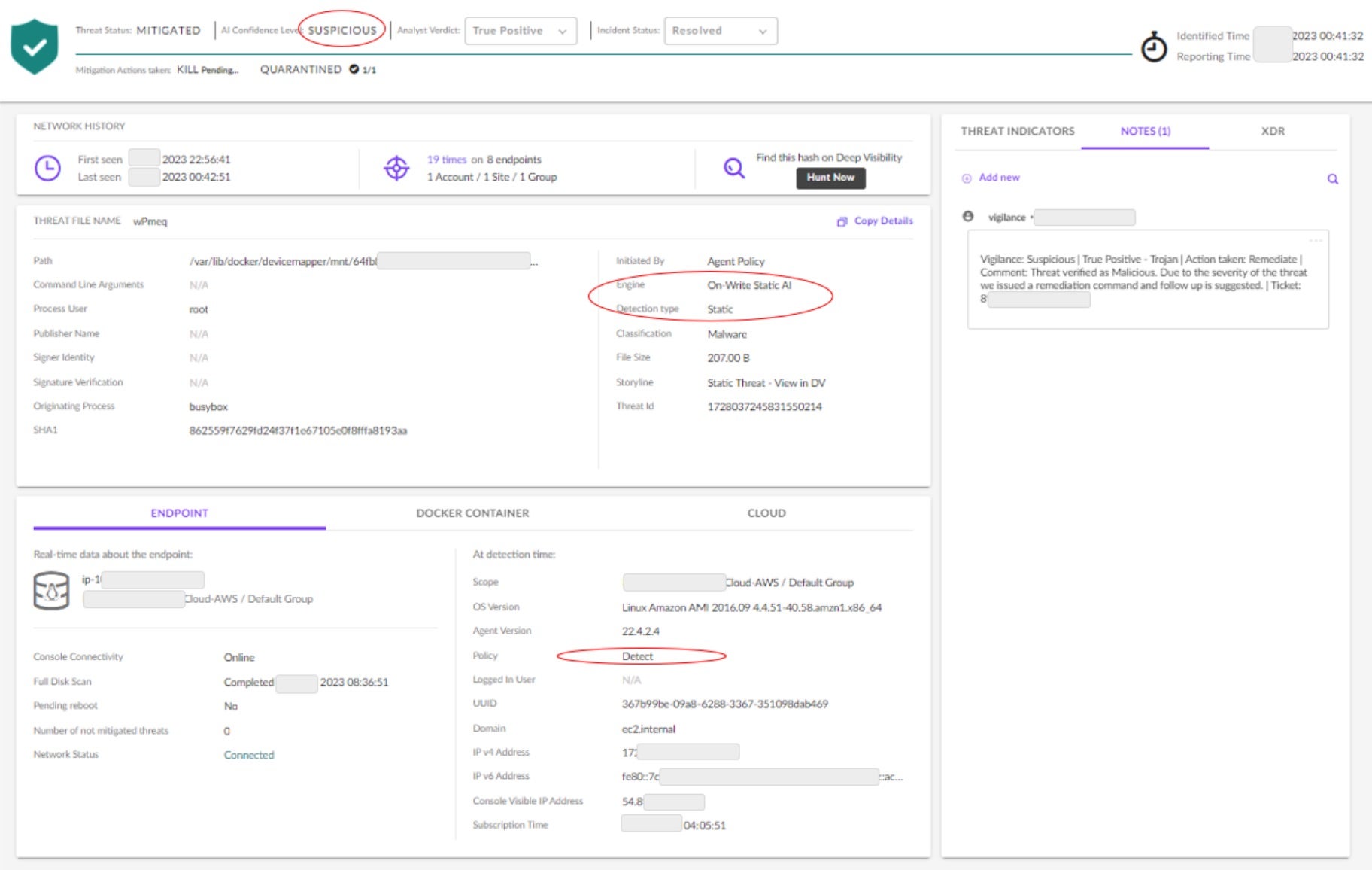
Maintain Deep Visibility Through Real-Time Monitoring
Deep system and network visibility, coupled with real-time monitoring, detection, and response capabilities, are security essentials for the energy sector. Advanced security solutions such as autonomous and AI-powered XDR can offer a comprehensive view of both IT and OT environments, enabling security teams to shave off minutes when identifying anomalies and potential cyber threats.
In an era of evolving and sophisticated attacks, such as ransomware and state-sponsored intrusions, real-time monitoring ensures that any unusual activity is quickly detected, allowing for immediate action and remediation as needed. This proactive approach is critical in safeguarding critical energy infrastructure against cyber threats that could disrupt operations and endanger public safety.
Stay Up-to-Date with Government Guidelines & Resources
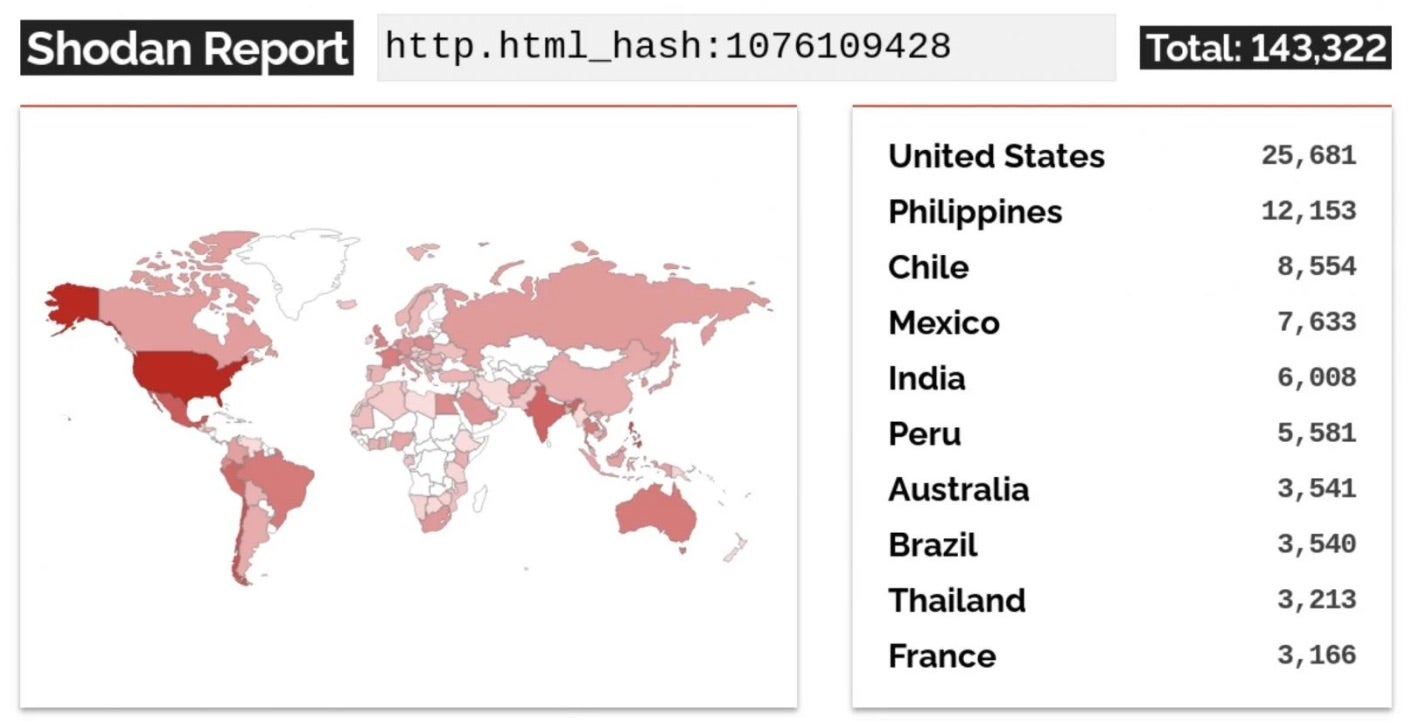
Legacy OT assets are designed without robust defenses against malicious cyber activities. Easy access to unsecured assets, wide availability of open-sourced device information (e.g. Shodan and Kamerka), and oft-deployed exploits accessible through frameworks like Metasploit, Core Impact, and Immunity Canvas, have all created a perfect storm of factors leading to increased cyber intrusion. To combat these growing risks, the U.S. government continues to urge energy and utilities providers to improve the resilience of their systems.
Following CISA’s latest warnings of increased exposure of OT systems to cyberattacks, the NSA published new resources this month to help organizations using SNORT improve their threat hunting. Called ‘ELITEWOLF’, the repository contains various ICS/SCADA (supervisory control and data acquisition)/OT-focused signatures and analytics to support critical suppliers as they implement continuous monitoring measures.
In addition to the new repository, CISA, FBI, NSA, and the U.S. Department of the Treasury also released guidance for OR vendors and other critical infrastructure facilities, focusing on how to minimize risk when using open-source software (OSS) in OT products.
Conclusion
Given their central role in powering economies, physical infrastructure, and digital systems, global energy and utility service providers have had to consider how to defend against a new wave of cyber adversaries in the last few years. Recent shifts in geopolitics have also added a new layer of complexity to this threat landscape, further highlighting the need for enhanced cybersecurity measures.
To thwart these threats and safeguard critical power grids and pipelines, energy and utility providers are increasingly looking to adopt a proactive and adaptive cybersecurity approach. This entails comprehensive risk assessments, robust detection and response systems, and building safer standards for working with third-parties vendors.
SentinelOne is ready to stand by organizations in the energy sector by managing the evolving attack surface before attacks can happen. Contact us or request a demo to learn how our AI-powered, autonomous XDR platform, Singularity , provides protection to the nation’s critical power service providers.
, provides protection to the nation’s critical power service providers.