Endpoint, Identity and Cloud | Top Cyber Attacks of 2023 (So Far)
2023 has been no stranger to cyber threats and both the rates and sophistication of attacks launched have only continued on their upward trajectories. Based on findings from a recent Cyber Threat Intelligence Index report, threats like ransomware, data breaches, and software vulnerabilities have all made major impacts on the landscape this year. As global enterprises have scaled up the amount of data they produce and store, threat actors have kept a watchful eye for new opportunities for attack.
In this post, learn about some of the most pressing cyber threats seen targeting the endpoint, identity, and cloud surfaces from the first three quarters of this year. By dissecting the causes and impacts of these notable attacks, enterprise and security leaders can better secure their data, systems, and networks against advanced threats down the line.
Endpoint-Based Attacks
Endpoint attacks have evolved into a critical concern, posing substantial threats to businesses across all industry verticals. As the amount of endpoints multiply and remote work opportunities continue to be the norm, the endpoint attack surface expands and leaves organizations vulnerable to a range of threats.
Attacks on endpoints exploit vulnerabilities within privileged computers, smartphones, and internet of things (IoT) devices. Major threats that loom over the endpoint attack surface include ransomware, phishing scams, zero-day exploits, fileless malware, and Denial-of-Service (DoS) attacks.
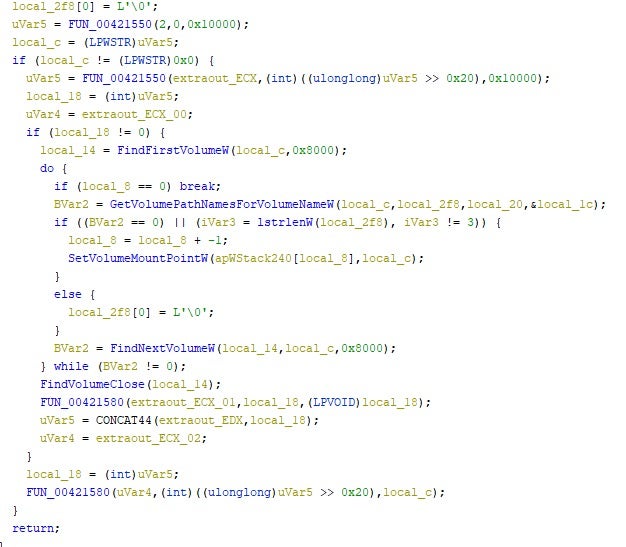
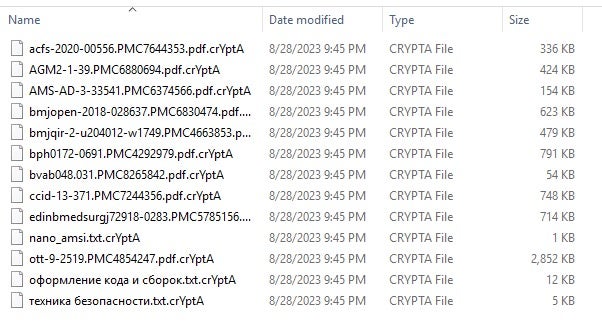
Ransomware Attacks
In the first three quarters of 2023, ransomware has targeted multiple critical infrastructure and major companies, including those listed below:
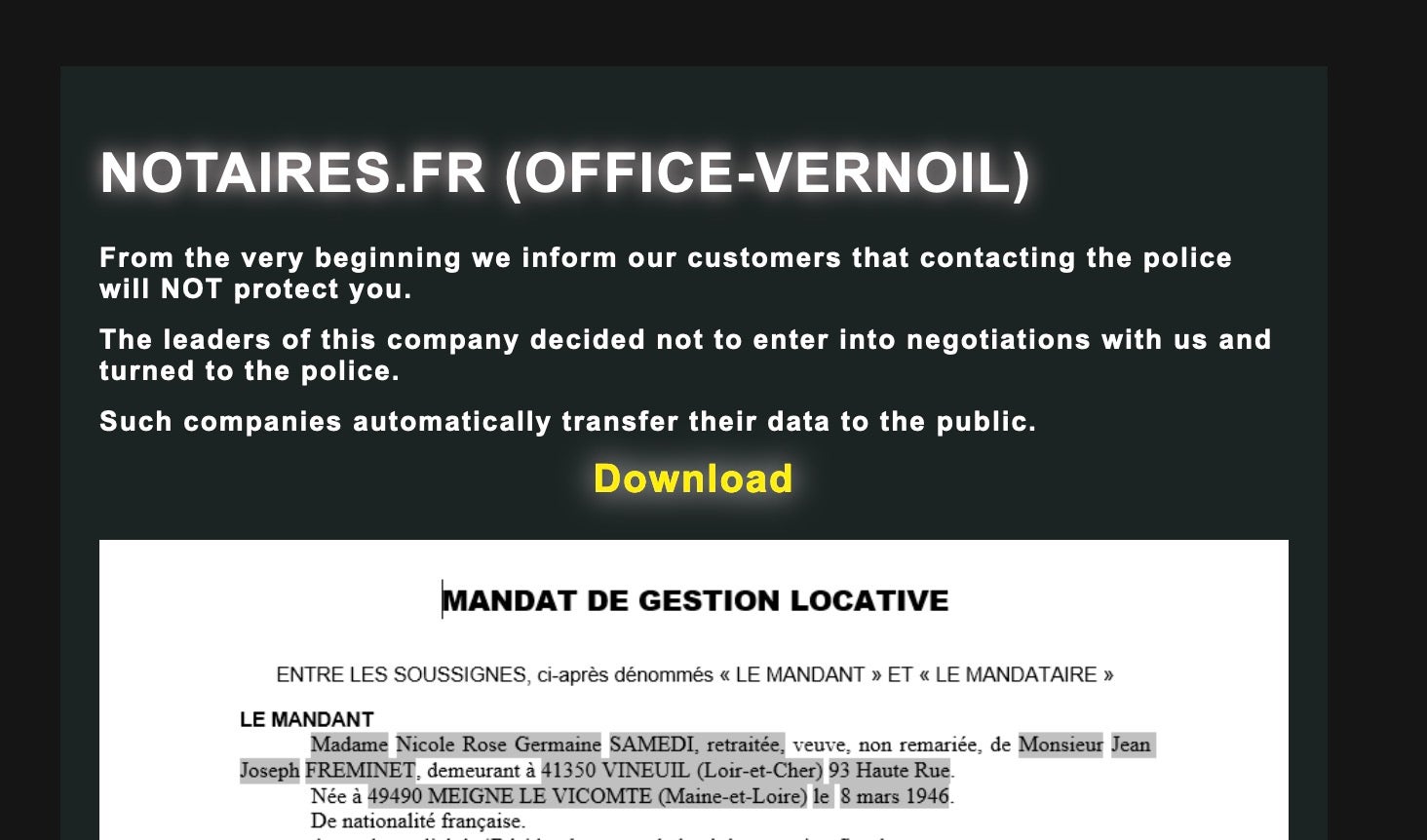
- San Francisco’s Bay Area Rapid Transit (Vice Society) – San Francisco’s BART was hit in January by a ransomware attack claimed by the Vice Society group. While no service disruption occurred, stolen data was posted online. BART confirms no impact on services or internal systems, but concerns from the incident have arisen due to potential backdoor access to critical systems.
- Reddit (BlackCat Ransomware) – ALPHV ransomware group, also known as BlackCat, claimed responsibility for a February cyberattack on Reddit. The attack, initiated through a successful phishing campaign, resulted in the theft of 80GB of data, including internal documents, source code, and employee and advertiser information. The group had announced its intent to leak the stolen data after failed attempts to extort $4.5 million from Reddit for its deletion.
- Dole Food Company – Dole Food Company confirmed a ransomware attack that occurred in February, which compromised an undisclosed number of employee records. While the impact was limited, production plants in North America were temporarily shut down due to the attack. The incident affected Dole’s workforce data, as reported in their annual filing with the SEC.
- United States Marshals Service (USMS) – Described as a major incident, the ransomware attack on the US Marshals Service, a federal law enforcement agency within the Department of Justice, compromised sensitive law enforcement data, including legal process returns, administrative data, and personally identifiable information (PII) of subjects associated with USMS investigations, third parties, and certain USMS employees.
- City of Oregon (Royal Ransomware) – In May, the City of Oregon encountered a ransomware attack when county data was encrypted. Election and 911 dispatch remained under control, but all other government operations were impacted. Restoring systems were calculated at the cost of millions for software reloads and network reconstruction. Claimed by Royal Ransomware, the attackers demanded a ransom for data access, with the specific amount not disclosed by county officials.
- Enzo Biochem – The New York-based biotech company suffered a ransomware attack in April compromising test data and personal information of approximately 2.5 million individuals. Names, test data, and 600,000 social security numbers were accessed. The attack on Enzo closely followed a separate attack on pharmacy giant, PharMerica, in May that saw the sensitive data of nearly 6 million people exposed.
So far, the FBI, CISA, and NSA, in partnership with other enforcement agencies, have issued the following joint cybersecurity advisories on the following ransomware in the past three quarters:
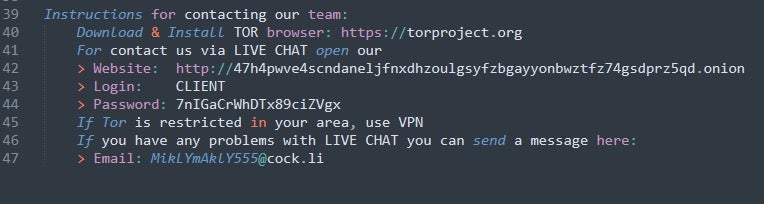
- Royal – Cybercriminals have targeted US and international organizations with Royal ransomware since September 2022. After infiltrating networks, they disable antivirus and exfiltrate data before deploying ransomware. Ransom instructions come after encryption via a .onion URL, demanding varied amounts from $1M to $11M in Bitcoin. Royal ransomware has been observed targeting critical sectors like manufacturing, communications, healthcare, and education.
- LockBit 3.0 – LockBit 3.0 (aka LockBit Black) operations follow a Ransomware-as-a-Service (RaaS) model and is a more evasive and modular continuation of its predecessors LockBit and LockBit 2.0. Affiliates that use LockBit 3.0 have been seen employing a variety of TTPs to attack a wide range of businesses in critical infrastructure sectors.
- BianLian – BianLian is a cybercriminal group conducting ransomware attacks on US and Australian critical infrastructure since June 2022. Known for ransomware development, deployment, and data extortion, they often exploit valid Remote Desktop Protocol (RDP) credentials, utilize open-source tools for reconnaissance, and exfiltrate data using FTP, Rclone, or Mega. In 2023, BianLian shifted from using a double-extortion model to exfiltration-based extortion, threatening to release data if ransom isn’t paid. They have targeted professional services and property development sectors in previous campaigns.
- Cl0p – Since emerging in February 2019, CL0P ransomware has evolved and now operates as a Ransomware-as-a-Service (RaaS), initial access broker (IAB) selling access to compromised networks, and a large botnet operator targeting the financial sector. Initially known for double extortion, they changed tactics in 2021 to focus on data exfiltration. Cl0p has compromised over 3,000 U.S. and 8,000 global organizations.
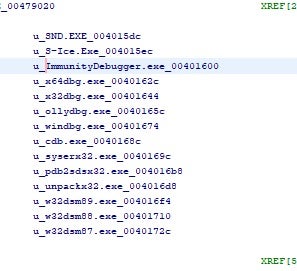
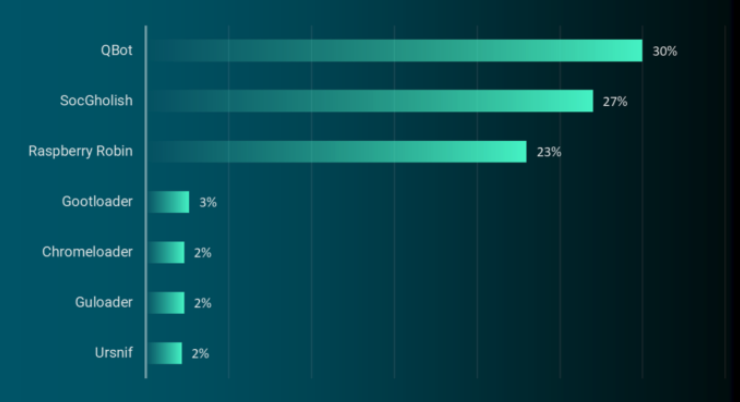
- QakBot – Also known as Qbot, Quackbot, Pinkslipbot, and TA750, Qakbot has caused numerous global malware infections since 2008. Initially a banking trojan, it evolved into a versatile botnet and malware variant used for reconnaissance, data exfiltration, lateral movement, and delivering ransomware. It targets various sectors, including financial and emergency services, commercial facilities, as well as the election infrastructure subsector, selling compromised device access to further affiliate threat actors’ goals.
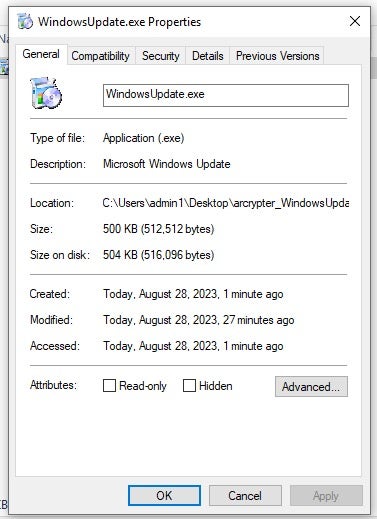
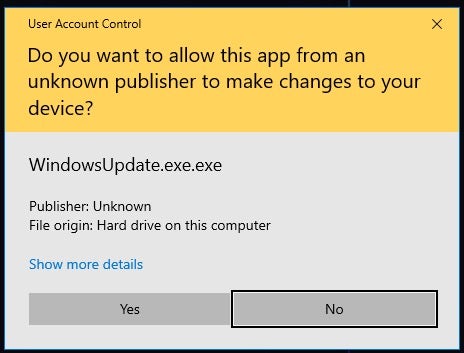
3CX Supply Chain Attack
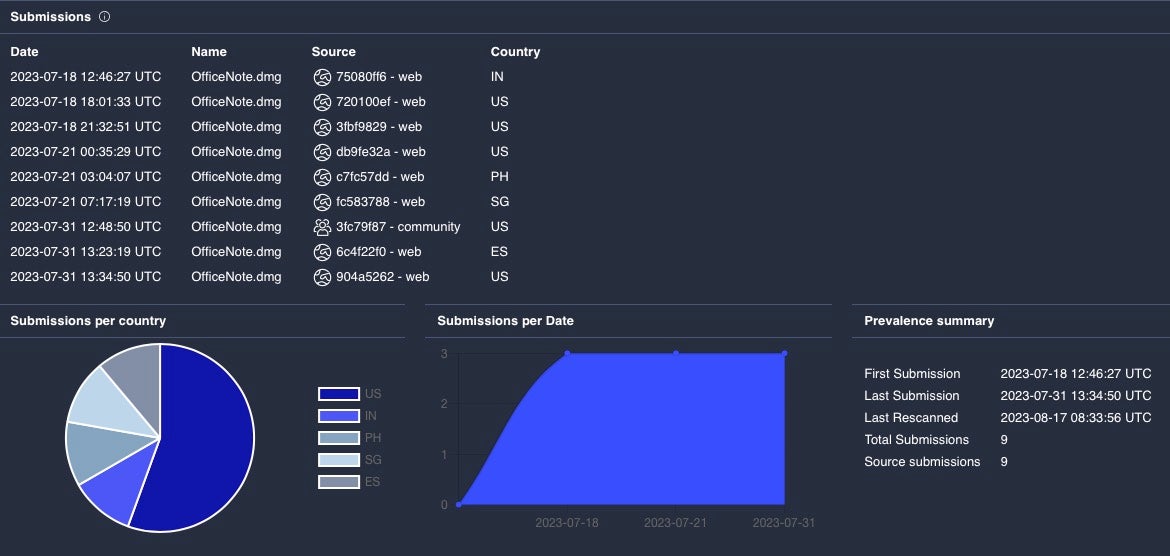
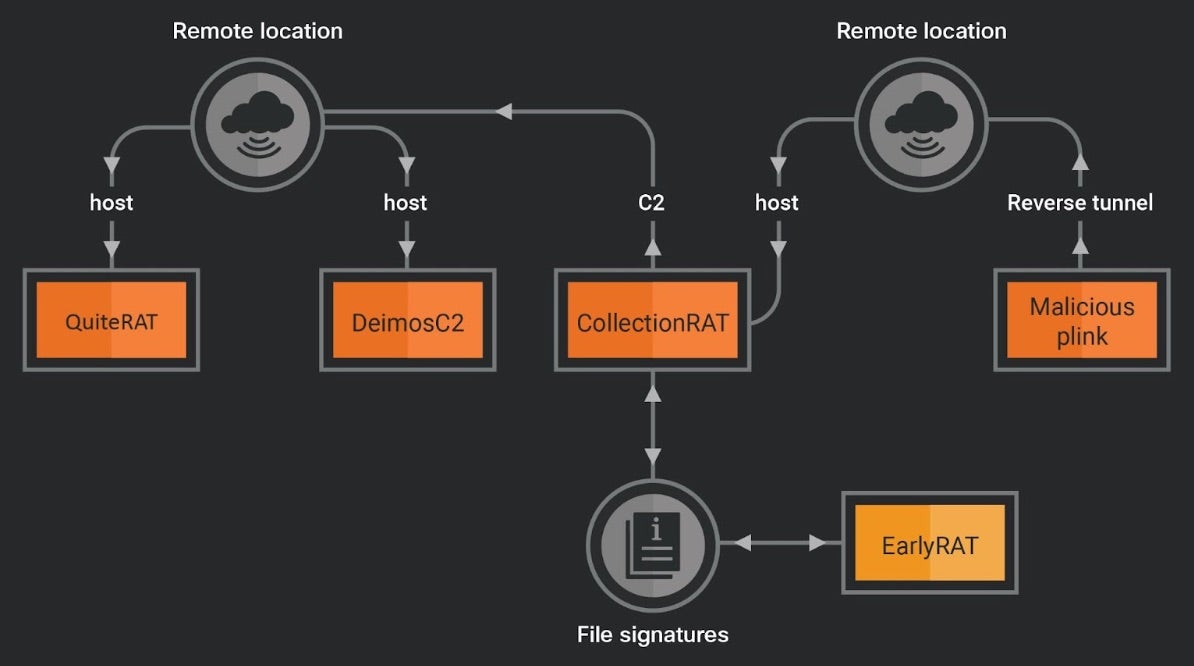
In a supply chain attack discovered in March dubbed “SmoothOperator”, actors associated with the North Korean regime compromised the infrastructure of the 3CX Private Automatic Branch Exchange (PABX) platform. The VoIP software development company is used by more than 600,000 globally and has over 12 million daily users including organizations across the automotive, food and beverage, hospitality, managed information technology service provider (MSP), and manufacturing industries.
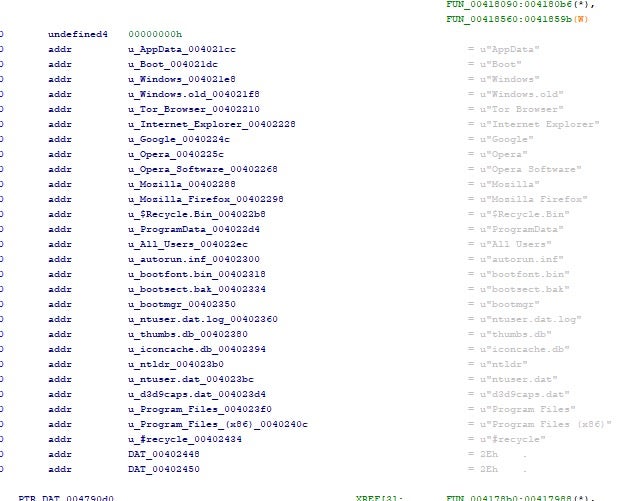
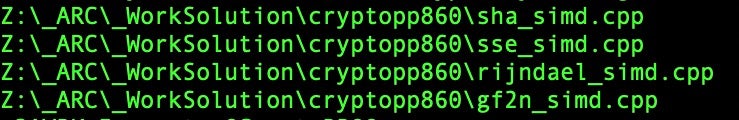
The actors used this access to insert malicious code into the 3CX endpoint clients, which were downloaded as updates by victims using the software. The backdoored version applied stealthy steganography by encoding a payload stub in an .ico image file hosted on a public code repository hosted at github[.]com/IconStorages/images, which let the malware obtain the active C2 server address. Long-reaching software supply chain attacks like these demonstrate how threat actors work innovatively to exploit network access and distribute malware.
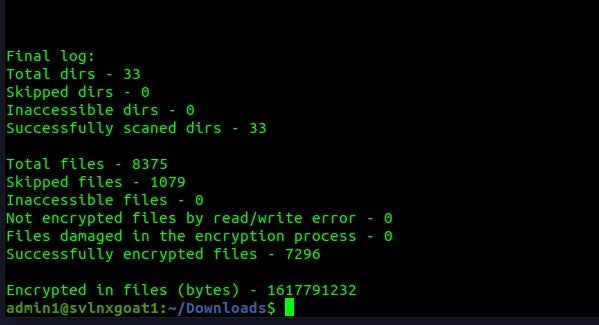
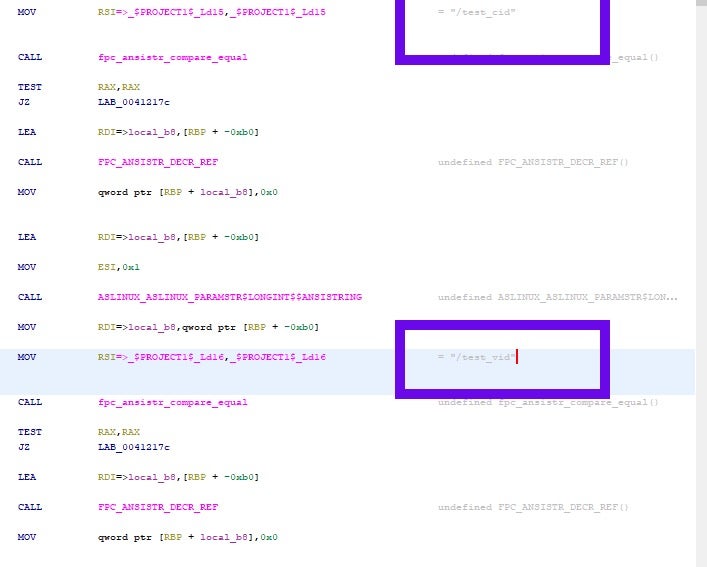
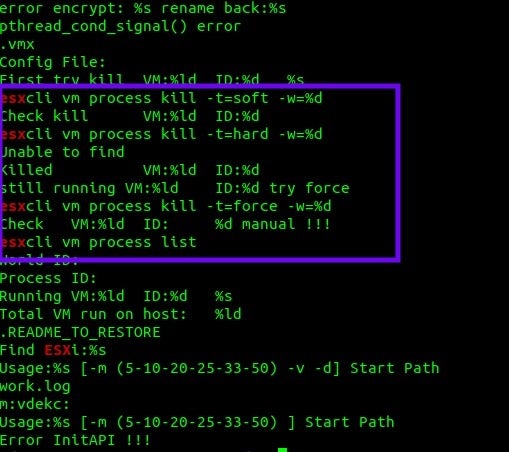
ESXi & Linux Ransomware
Ransomware groups such as AvosLocker, Black Basta, BlackMatter, Hello Kitty, LockBit, RansomEXX, REvil, and the now-defunct Hive have all continued to target VMware ESXi servers throughout 2023. Since 2021, organized ransomware groups have expanded targeting to include Linux systems thanks to the high likelihood of critical services or sensitive data. Disruption of Linux systems can lead to service outages, placing increased pressure on victims to pay a ransom.
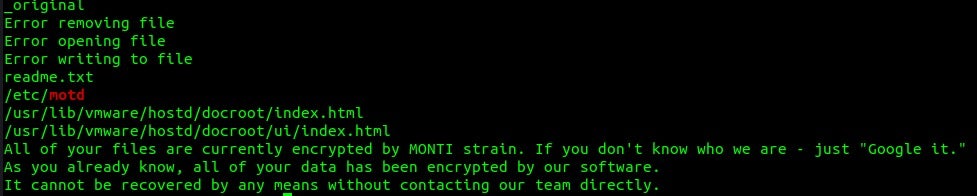
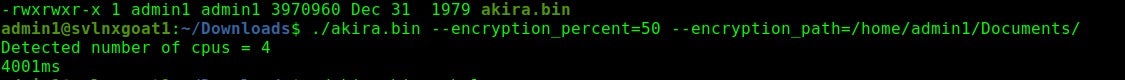
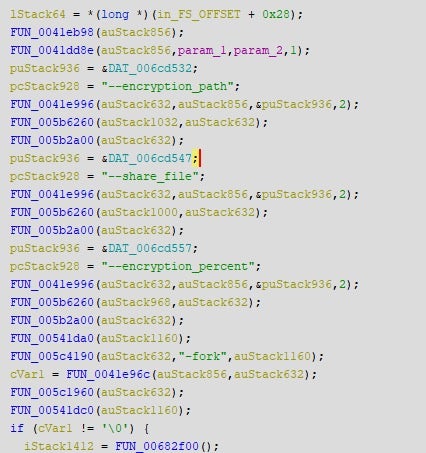
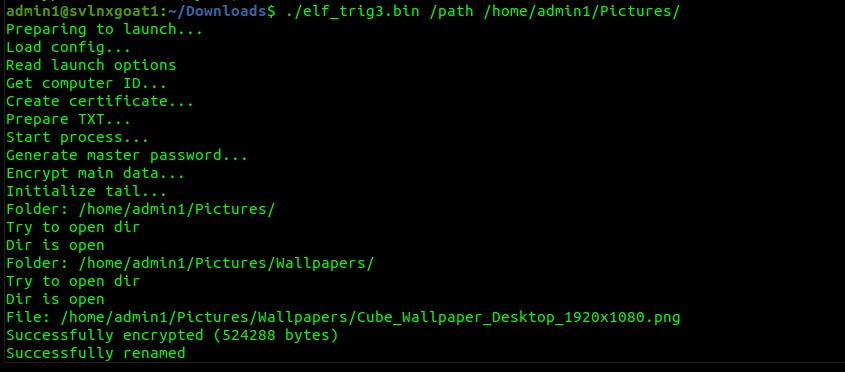
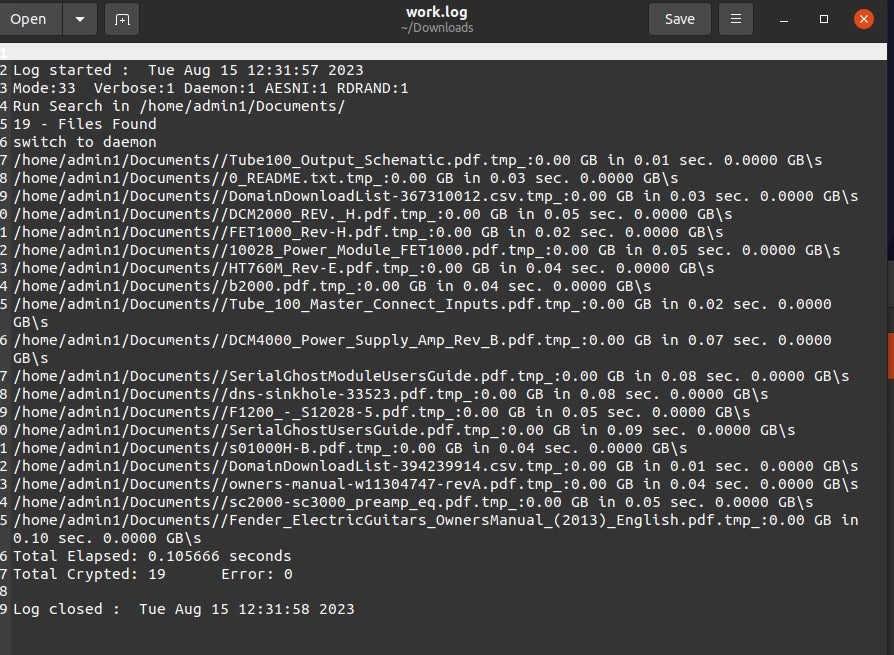
These attacks often target the intersection of endpoint and cloud services, including on-premises Linux servers and hypervisors like VMWare ESXi. SentinelLabs’ research found that the availability of Babuk ransomware source code has made an outsized impact on the ESXi threat landscape. Many other Linux families are proliferating, including recent Linux additions by actors behind Abyss, Akira, Monti, and Trigona.
Identity-Based Attacks
Targeting the core of digital trust and authentication, identity-based attacks continue to rise in the cyber threat landscape. These attacks exploit weaknesses in user identities, credentials, and authentication processes and seek to gain unauthorized access to sensitive data and systems.
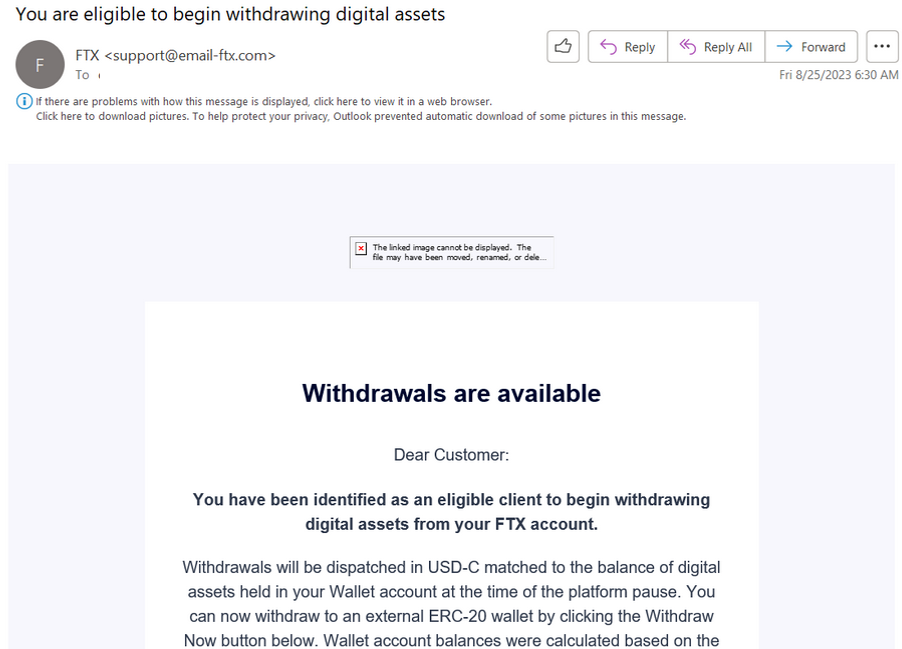
Enterprises around the world have exponentially grown the number of digital identities used in day-to-day operations, each one widening this attack surface. These identities are most vulnerable to threats such as phishing (and all of its variations), credential stuffing, identity theft, (fueled by social engineering), and attacks on single-sign-on (SSO) systems and multi-factor authentication (MFA) protocols.
Microsoft Exchange Online & Azure AD Vulnerability
This summer, details emerged on attacks against several US government agencies by an actor tracked as STORM-0558, a China-aligned espionage-motivated actor. The attacks abused several components to Microsoft permissions, including broad application scopes and a stolen signing key, which enabled the actors to mint session tokens to affected organizations’ Microsoft services. The original reports suggested only Exchange Online was impacted, though researchers found the flaw impacted other types of Azure Active Directory applications, including all applications that support individual (non-organization) account authentication.
BingBang
BingBang is an issue in Azure Active Directory (AD) application scopes where the default configuration may expose applications to undesired access. Researchers found that the default configuration for many Azure applications meant that any Azure AD user could access applications.
To remediate the issues outlined in BingBang, organizations using Azure AD authentication should verify what levels of access are delegated to applications, focusing first on sensitive and critical applications.
Cloud-Based Attacks
Cloud-based attacks continue to be a prominent and concerning trend, targeting vulnerabilities within cloud technologies and infrastructures. These attacks aim to compromise sensitive data housed by enterprise businesses, disrupt operations, or gain unauthorized access.
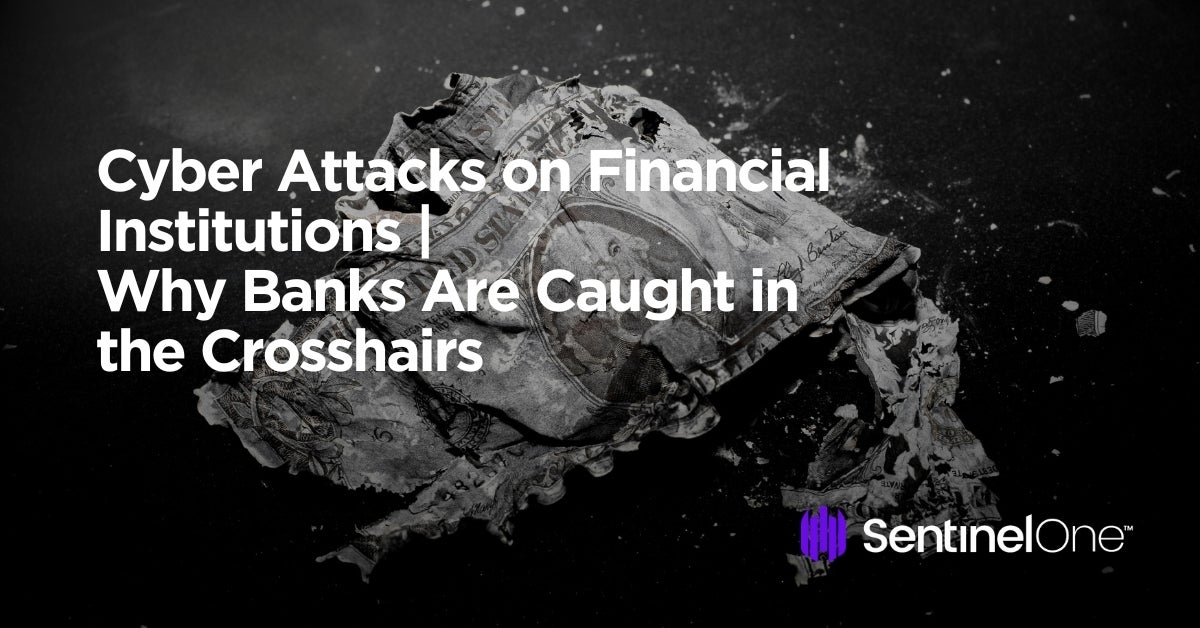
Cloud environments are vulnerable to threat actors working to exploit weak access controls to infiltrate cloud repositories. Distributed-Denial-of-Service (DDoS) attacks, capable of overwhelming cloud servers and causing widespread service disruptions, are also a major threat to modern clouds. Most notably in 2023, there has been a significant increase in cloud infostealers where financially motivated tools steal data from vulnerable or misconfigured cloud environments.
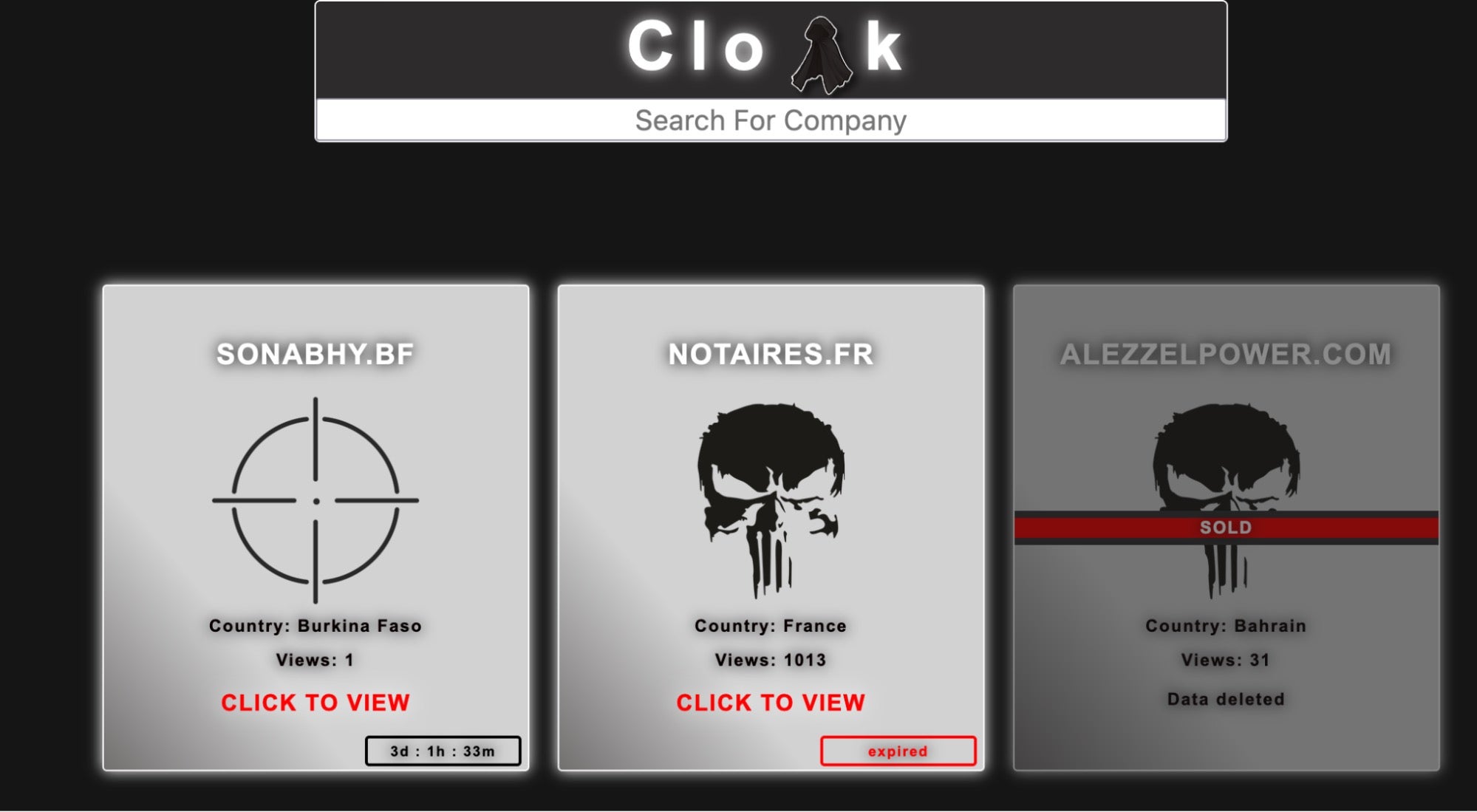
Cl0p Ransomware
In May 2023, the Cl0p (aka Clop) ransomware group made waves by exploiting a zero-day vulnerability in the MOVEit file transfer server application, which runs on Windows servers. The exploit chain delivers a Microsoft Internet Information Services (IIS) .aspx webshell to the server’s MOVEitTransferwwwroot directory, which steals files from the server as well as connected Azure Blob Storage. SentinelOne’s report provides queries that organizations can use to identify potential exploitation by the Cl0p group.
The attack demonstrated a significant shift where traditionally endpoint-focused ransomware actors wrote code specifically to target cloud storage services. The impact was massive, with more than 500 organizations and the data of 34 million individuals compromised, making it one of the biggest threat campaigns of 2023.
Cloud Infostealers
Throughout 2023, there has been a consistent rise in prevalence of cloud infostealers, which seek credentials from misconfigured or vulnerable cloud services. Some notable examples include:
- AlienFox – AlienFox is a comprehensive tool built on Androxgh0st code snippets and sold through Telegram channels. Attackers run the modular, Python-based toolset remotely against exposed cloud services. AlienFox primarily targets credentials that attackers can abuse to conduct spam attacks, API keys, and secrets from popular services including AWS SES and Microsoft Office 365. A comprehensive breakdown of targeted services can be found in SentinelLabs’ full report.
- Legion – An offshoot from the same code origin as AlienFox, Legion shares much of the same, spam-centric features. Like AlienFox, Legion is distributed to buyers who frequent Telegram channels.
- TeamTNT Doppelgänger – The infamous TeamTNT seemingly returned in 2023 with a cloud stealer that targets credentials from a variety of popular cloud and development services. While attribution remains difficult with publicly available tools like these, the actor behind recent campaigns has demonstrated active development and adaptation to new attack surfaces, such as Google Cloud and Azure service account credentials. These recent campaigns use dynamic DNS hosting provider AnonDns for command-and-control (C2). Most of the tools are Bash or Shell scripts, though the group occasionally leverages binaries, such as a Golang executable (SHA1:
2ed9517159b89af2518cf65a93f3377dea737138) that enables propagation. The recent campaigns suggest the actor may have different motives. While the original TeamTNT prolifically delivered cryptocurrency mining malware with a minor focus on credential harvesting, the newer campaigns conduct more credential harvesting and environment enumeration than cryptomining.
Conclusion | How SentinelOne Measures Up to 2023 Cyber Attacks
Instability within the geopolitical and economic landscape have all led to significant challenges in securing global enterprises this year. What’s clear from the attacks listed in this blog post is that transnational and organized cyber criminals continue to develop their threat operations to execute high-impact attacks by extorting ransoms, disrupting governments and critical services, and exposing sensitive data. Continuing to share threat intelligence on past and ongoing threats allows security and enterprise leaders to better understand where their gaps and weaknesses are so as to prepare for similar attacks in the future.
Facing these challenges, business leaders this year are much more aware of their organizations’ cyber risks than they were in 2022 and, most importantly, more willing to address them. Leaders are focused on minimizing business disruption and reputational damage and devoting more resources than before to bolstering day-to-day cyber defenses. This encompasses the strengthening of controls around third-party access, establishing cyber risk management and accountability, as well as investing in advanced cybersecurity solutions.
SentinelOne is trusted by enterprises in every industry vertical, providing the protection they need to stay ahead of modern threat actors. In one platform, SentinelOne’s Singularity XDR unites endpoint, identity, and cloud protection into an efficient cybersecurity solution. Request a demo or contact us to learn more about how Singularity leverages the power of AI to detect and respond to today’s threats.



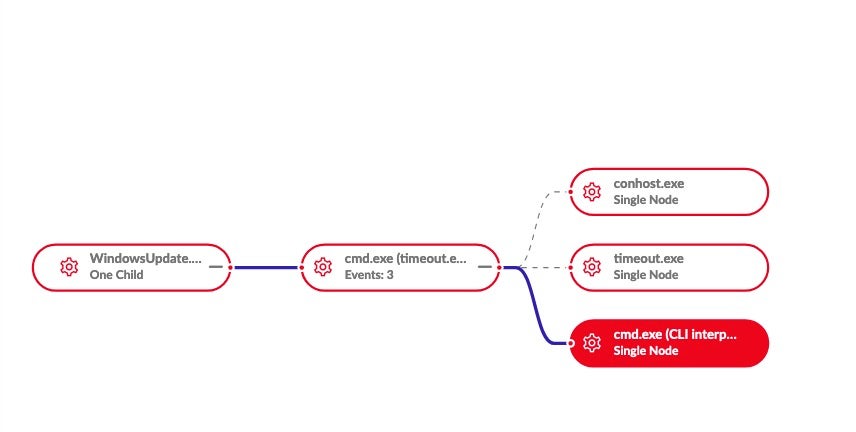
 view of calls to timeout.exe (delayed execution/evasion)
view of calls to timeout.exe (delayed execution/evasion)