When Efforts to Contain a Data Breach Backfire
Earlier this month, the administrator of the cybercrime forum Breached received a cease-and-desist letter from a cybersecurity firm. The missive alleged that an auction on the site for data stolen from 10 million customers of Mexico’s second-largest bank was fake news and harming the bank’s reputation. The administrator responded to this empty threat by purchasing the stolen banking data and leaking it on the forum for everyone to download.
On August 3, 2022, someone using the alias “Holistic-K1ller” posted on Breached a thread selling data allegedly stolen from Grupo Financiero Banorte, Mexico’s second-biggest financial institution by total loans. Holistic-K1ller said the database included the full names, addresses, phone numbers, Mexican tax IDs (RFC), email addresses and balances on more than 10 million citizens.
There was no reason to believe Holistic-K1ller had fabricated their breach claim. This identity has been highly active on Breached and its predecessor RaidForums for more than two years, mostly selling databases from hacked Mexican entities. Last month, they sold customer information on 36 million customers of the Mexican phone company Telcel; in March, they sold 33,000 images of Mexican IDs — with the front picture and a selfie of each citizen. That same month, they also sold data on 1.4 million customers of Mexican lending platform Yotepresto.
But this history was either overlooked or ignored by Group-IB, the Singapore-based cybersecurity firm apparently hired by Banorte to help respond to the data breach.
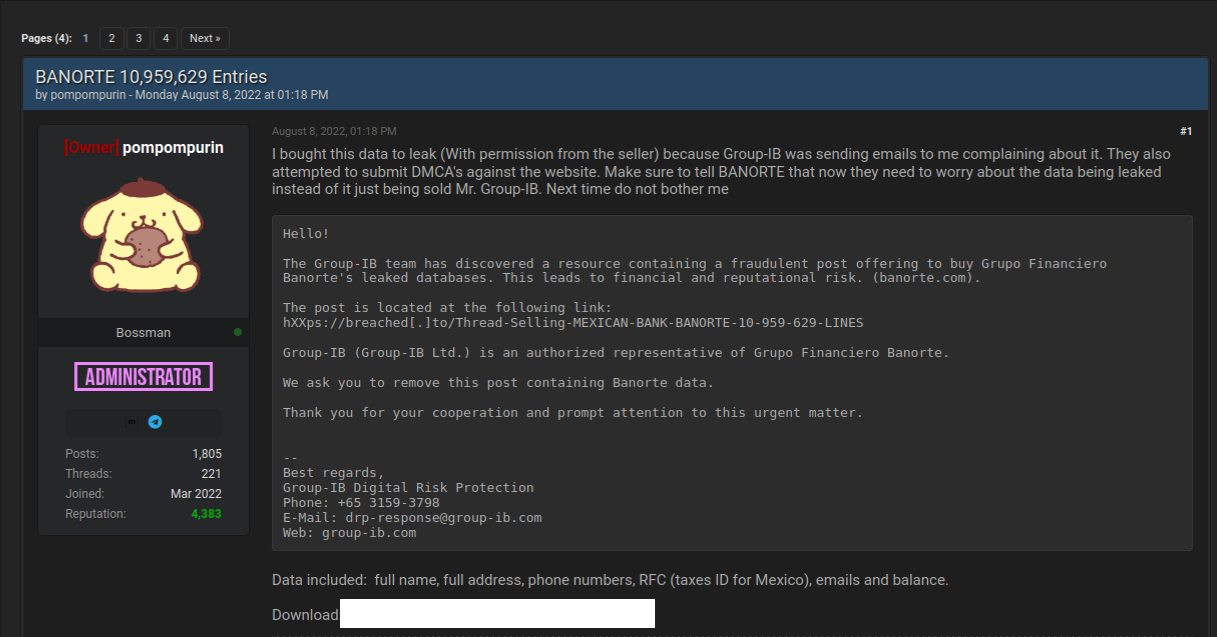
“The Group-IB team has discovered a resource containing a fraudulent post offering to buy Grupo Financiero Banorte’s leaked databases,” reads a letter the Breach administrator said they received from Group-IB. “We ask you to remove this post containing Banorte data. Thank you for your cooperation and prompt attention to this urgent matter.”
The administrator of Breached is “Pompompurin,” the same individual who alerted this author in November 2021 to a glaring security hole in a U.S. Justice Department website that was used to spoof security alerts from the FBI. In a post to Breached on Aug. 8, Pompompurin said they bought the Banorte database from Hacker-K1ller’s sales thread because Group-IB was sending emails complaining about it.
“They also attempted to submit DMCA’s against the website,” Pompompurin wrote, referring to legal takedown requests under the Digital Millennium Copyright Act. “Make sure to tell Banorte that now they need to worry about the data being leaked instead of just being sold.”
Banorte did not respond to requests for comment. Nor did Group-IB. But in a brief written statement picked up on Twitter, Banorte said there was no breach involving their infrastructure, and the data being sold is old.
“There has been no violation of our platforms and technological infrastructure,” Banorte said. “The set of information referred to is inaccurate and outdated, and does not put our users and customers at risk.”
That statement may be 100 percent true. Still, it is difficult to think of a better example of how not to do breach response. Banorte shrugging off this incident as a nothingburger is baffling: While it is almost certainly true that the bank balance information in the Banorte leak is now out of date, the rest of the information (tax IDs, phone numbers, email addresses) is harder to change.
“Is there one person from our community that think sending cease and desist letter to a hackers forum operator is a good idea?,” asked Ohad Zaidenberg, founder of CTI League, a volunteer emergency response community that emerged in 2020 to help fight COVID-19 related scams. “Who does it? Instead of helping, they pushed the organization from the hill.”
Kurt Seifried, director of IT for the CloudSecurityAlliance, was similarly perplexed by the response to the Banorte breach.
“If the data wasn’t real….did the bank think a cease and desist would result in the listing being removed?” Seifried wondered on Twitter. “I mean, isn’t selling breach data a worse crime usually than slander or libel? What was their thought process?”
A more typical response when a large bank suspects a breach is to approach the seller privately through an intermediary to ascertain if the information is valid and what it might cost to take it off the market. While it may seem odd to expect cybercriminals to make good on their claims to sell stolen data to only one party, removing sold stolen items from inventory is a fairly basic function of virtually all cybercriminal markets today (apart from perhaps sites that traffic in stolen identity data).
At a minimum, negotiating or simply engaging with a data seller can buy the victim organization additional time and clues with which to investigate the claim and ideally notify affected parties of a breach before the stolen data winds up online.
It is true that a large number of hacked databases put up for sale on the cybercrime underground are sold only after a small subset of in-the-know thieves have harvested all of the low-hanging fruit in the data — e.g., access to cryptocurrency accounts or user credentials that are recycled across multiple websites. And it’s certainly not unheard of for cybercriminals to go back on their word and re-sell or leak information that they have sold previously.
But companies in the throes of responding to a data security incident do themselves and customers no favors when they underestimate their adversaries, or try to intimidate cybercrooks with legal threats. Such responses generally accomplish nothing, except unnecessarily upping the stakes for everyone involved while displaying a dangerous naiveté about how the cybercrime underground works.




Leave a Reply
Want to join the discussion?Feel free to contribute!