With the recent demise of several popular “proxy” services that let cybercriminals route their malicious traffic through hacked PCs, there is now something of a supply chain crisis gripping the underbelly of the Internet. Compounding the problem, several remaining malware-based proxy services have chosen to block new registrations to avoid swamping their networks with a sudden influx of customers.
Last week, a seven-year-old proxy service called 911[.]re abruptly announced it was permanently closing after a cybersecurity breach allowed unknown intruders to trash its servers and delete customer data and backups. 911 was already akin to critical infrastructure for many in the cybercriminal community after its top two competitors — VIP72 and LuxSocks — closed or were shut down by authorities over the past 10 months.
The underground cybercrime forums are now awash in pleas from people who are desperately seeking a new supplier of abundant, cheap, and reliably clean proxies to restart their businesses. The consensus seems to be that those days are now over, and while there are many smaller proxy services remaining, few of them on their own are capable of absorbing anywhere near the current demand.
“Everybody is looking for an alternative, bro,” wrote a BlackHatForums user on Aug. 1 in response to one of many “911 alternative” discussion threads. “No one knows an equivalent alternative to 911[.]re. Their service in terms of value and accessibility compared to other proxy providers was unmatched. Hopefully someone comes with a great alternative to 911[.]re.”
NEW SOCKS, SAME OLD SHOES
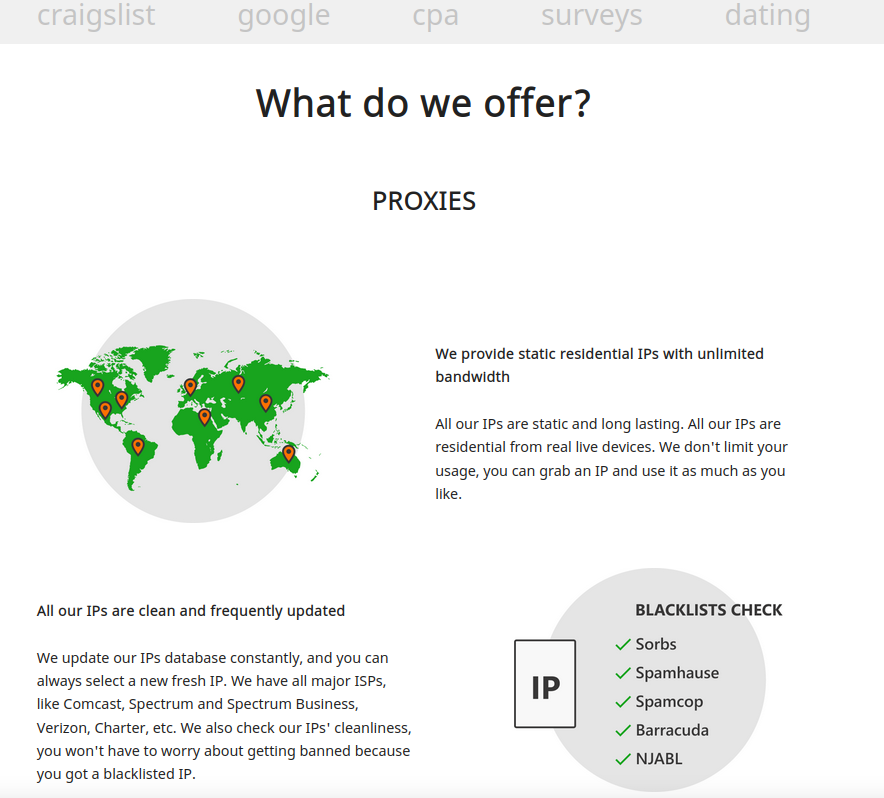
Among the more frequently recommended alternatives to 911 is SocksEscort[.]com, a malware-based proxy network that has been in existence since at least 2010. Here’s what part of their current homepage looks like:
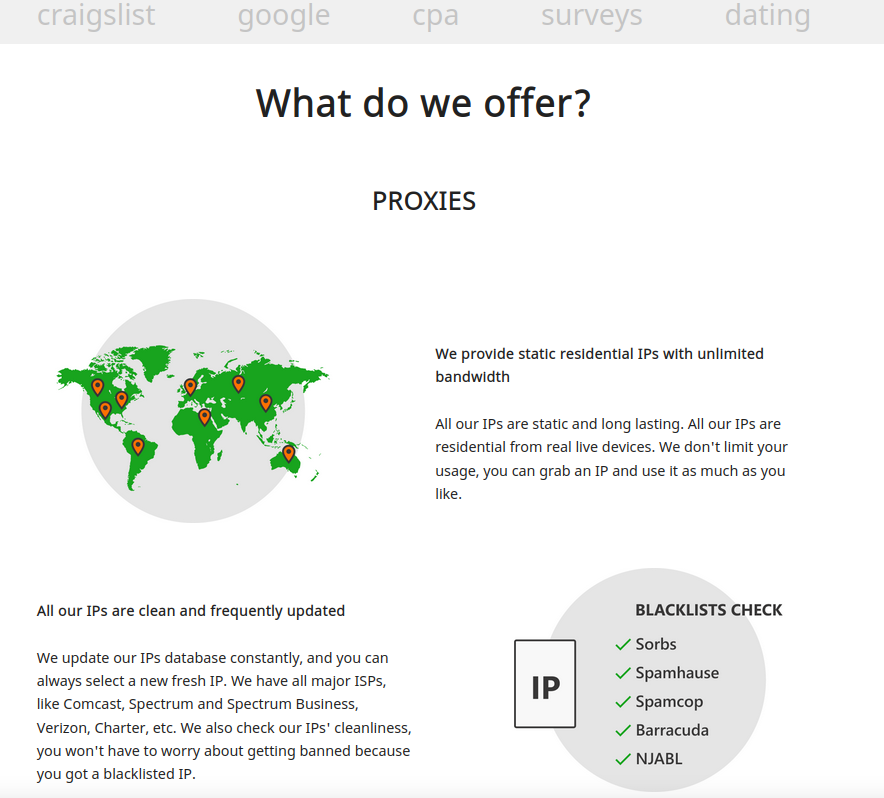
The SocksEscort home page says its services are perfect for people involved in automated online activity that often results in IP addresses getting blocked or banned, such as Craigslist and dating scams, search engine results manipulation, and online surveys.
But faced with a deluge of new signups in the wake of 911’s implosion, SocksEscort was among the remaining veteran proxy services that opted to close its doors to new registrants, replacing its registration page with the message:
“Due to unusual high demand, and heavy load on our servers, we had to block all new registrations. We won’t be able to support our proxies otherwise, and close SocksEscort as a result. We will resume registrations right after demand drops. Thank you for understanding, and sorry for the inconvenience.”
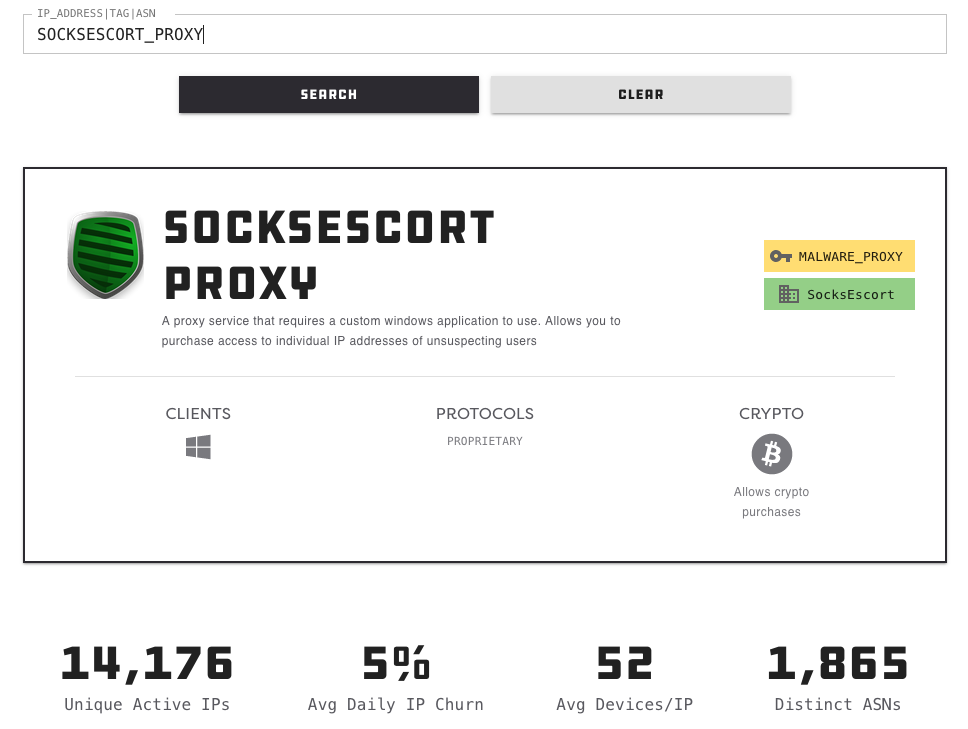
According to Spur.us, a startup that tracks proxy services, SocksEscort is a malware-based proxy offering, which means the machines doing the proxying of traffic for SocksEscort customers have been infected with malicious software that turns them into a traffic relay.
Spur says SocksEscort’s proxy service relies on software designed to run on Windows computers, and is currently leasing access to more than 14,000 hacked computers worldwide. That is a far cry from the proxy inventory advertised by 911, which stood at more than 200,000 IP addresses for rent just a few days ago.
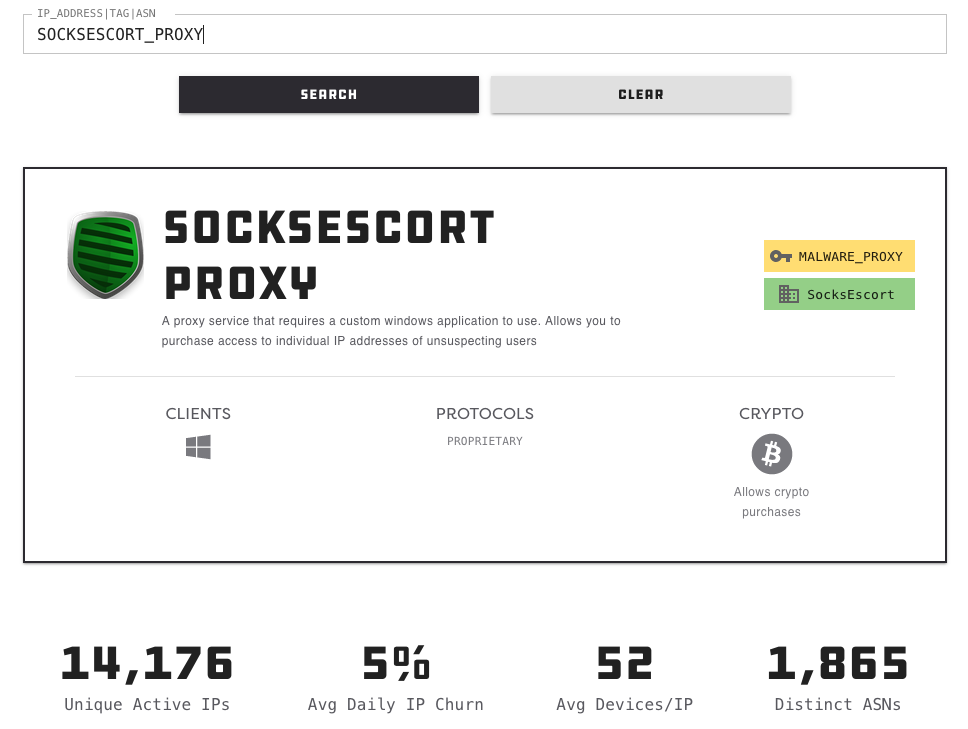
Image: Spur.us
SocksEscort is what’s known as a “SOCKS Proxy” service. The SOCKS (or SOCKS5) protocol allows Internet users to channel their Web traffic through a proxy server, which then passes the information on to the intended destination. From a website’s perspective, the traffic of the proxy network customer appears to originate from a rented/malware-infected PC tied to a residential ISP customer, not from the proxy service customer.
These services can be used in a legitimate manner for several business purposes — such as price comparisons or sales intelligence — but they are massively abused for hiding cybercrime activity because they make it difficult to trace malicious traffic to its original source.
The disruption at 911[.]re came days after KrebsOnSecurity published an in-depth look at the long-running proxy service, which showed that 911 had a history of incentivizing the installation of its proxy software without user notice or consent, and that it actually ran some of these “pay-per-install” schemes on its own to guarantee a steady supply of freshly-hacked PCs.
That story also showed once again that the people who are building and leasing these botnets are surprisingly easy to identify in real life, particularly given that they operate malware-based anonymity services that enable a great deal of cybercrime activity.
Such was the case again with SocksEscort. Hilariously, the common link that exposed the real-life identities of the people running this SOCKS service was that they all worked for the same online shoe store.
ANGRY CODERS
SocksEscort[.]com was originally registered to the email address “michdomain@gmail.com,” which according to DomainTools.com was used to register a handful of related domains, including its previous incarnation — super-socks[.]biz. Cached versions of the site show that in 2010 the software which powers the network was produced with a copyright of “Escort Software.”
Super-socks[.]biz came online around the same time as another domain registered to that “michdomain” email: ip-score[.]com, which soon became shorthand on several cybercrime forums for a service that could tell visitors whether their Internet address — or more precisely, the proxy they were using — was flagged by any security software or services as compromised or malicious.
IP-score offered a revenue sharing program for websites that chose to embed its IP-scoring code, and the copyright on that userbar program was “Angry Coders.”

A copy of ip-score.com, as indexed by Archive.org.
A review of the Internet addresses historically used by Super-socks[.]biz and SocksEscort[.]com reveals that these domains at various times over the years shared an Internet address with a small of other domains, including angrycoders[.]net, iskusnyh[.]pro, and kc-shoes[.]ru.
Cached copies of angrycoders[.]net from the Wayback Machine don’t reveal much about this particular group of irate programmers, but a search on the domain brings up several now-dormant listings for an Angry Coders based in Omsk, a large city in the Siberian region of Russia. The domain was registered in 2010 to an Oleg Iskushnykh from Omsk, who used the email address iboss32@ro.ru.
According to Constella Intelligence [currently an advertiser on KrebsOnSecurity], Oleg used the same password from his iboss32@ro.ru account for a slew of other “iboss” themed email addresses, one of which is tied to a LinkedIn profile for an Oleg Iskhusnyh, who describes himself as a senior web developer living in Nur-Sultan, Kazakhstan.
Iskusnyh’s Github profile shows he has contributed code to a number of online payment-related technologies and services, including Ingenico ePayments, Swedbank WooCommerce, Mondido Payments, and Reepay.
DON’T JUDGE A MAN UNTIL YOU’VE WALKED A MILE IN HIS SOCKS
The various “iboss” email accounts appear to have been shared by multiple parties. A search in Constella’s database of breached entities on “iboss32@gmail.com” reveals someone using the name Oleg Iskusnyh registered an online profile using a phone number in Bronx, New York. Pivoting on that phone number — 17187154415 — reveals a profile exposed in the breach at sales intelligence firm Apollo with the first name “Dmitry” who used the email address chepurko87@gmail.com.
That email is connected to a LinkedIn profile for a Dmitry Chepurko in Pavlodar, Kazakhstan. Chepurko’s resume says he’s a full stack developer, who most recently worked in the Omsk offices of a German shoe company called KC Shoes (the aforementioned kc-shoes.ru]. Chepurko’s resume says before that he worked on his own for a decade using the freelancing platform Upwork.
The Upwork profile listed in Chepurko’s LinkedIn C.V. is no longer active. But that same now-defunct Upwork account link is still listed as the profile of a “Dmitry C.” in an UpWork profile page for the Angry Coders team in Omsk, Russia.
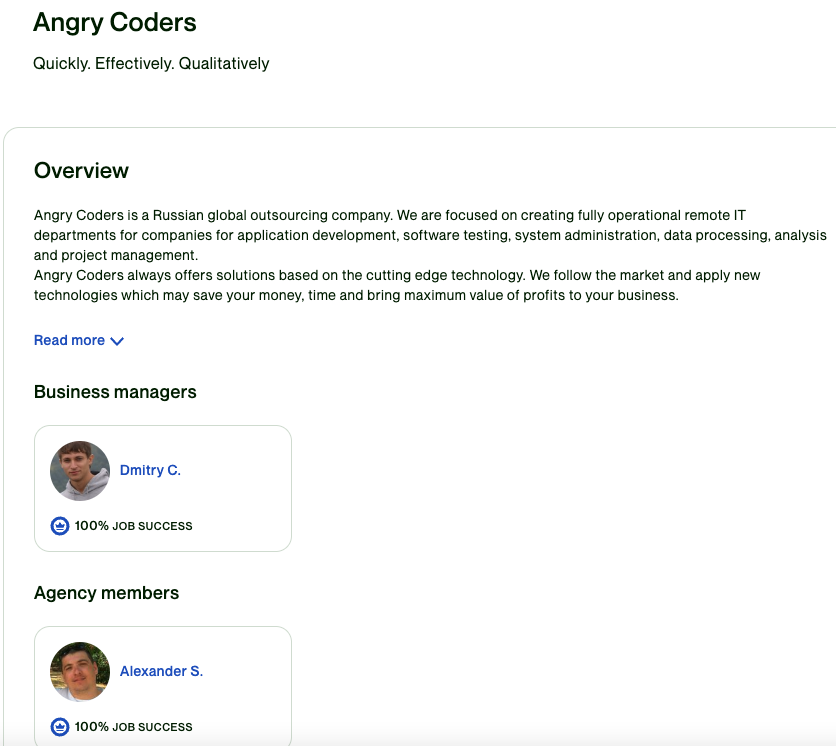
The UpWork profile page for the Angry Coders programming team from Omsk, RU.
Who is the “Alexander S.” listed above under the “Agency members” heading in the Upwork profile for Angry Coders? Historical DNS records from Farsight Security show angrycoders.net formerly included the subdomain “smollalex.angrycoders[.]net”.
A simple Internet search on “kc-shoes” reveals a Github account for a user from Omsk with the first name Alexander and the account name “Smollalex.” Alexander’s Github account indicates he has contributed code to the kc-shoes website as well.
Constella’s service shows that “Smollalex” was a favorite handle chosen by an Alexandr Smolyaninov from Omsk. The Smollalex Github account associates this individual with a company in Omsk that sells parts for oil and gas pipelines.
That shoes are apparently the common link among the Angry Coders responsible for SocksEscort is doubly amusing because — at least according to the posts on some cybercrime forums — one big reason people turn to these proxy services is for “shoe botting” or “sneaker bots,” which refers to the use of automated bot programs and services that aid in the rapid acquisition of limited-release, highly-sought-after designer athletic shoes that can then be resold at huge markups on secondary markets.
It’s not clear if the Angry Coders team members remain affiliated with SocksEscort; none of them responded to requests for comment. There were certain connections made clear throughout the research mentioned above that the Angry Coders outsourced much of the promotion and support of their proxy service to programmers based in India and Indonesia, where apparently a large chunk of its customers currently reside.
Further reading:
July 29, 2022: 911 Proxy Service Implodes After Disclosing Breach
July 28, 2022: Breach Exposes Users of Microleaves Proxy Service
July 18, 2022: A Deep Dive Into the Residential Proxy Service ‘911’
June 28, 2022: The Link Between AWM Proxy & the Glupteba Botnet
June 22, 2022: Meet the Administrators of the RSOCKS Proxy Botnet
Sept. 1, 2021: 15-Year-Old Malware Proxy Network VIP72 Goes Dark



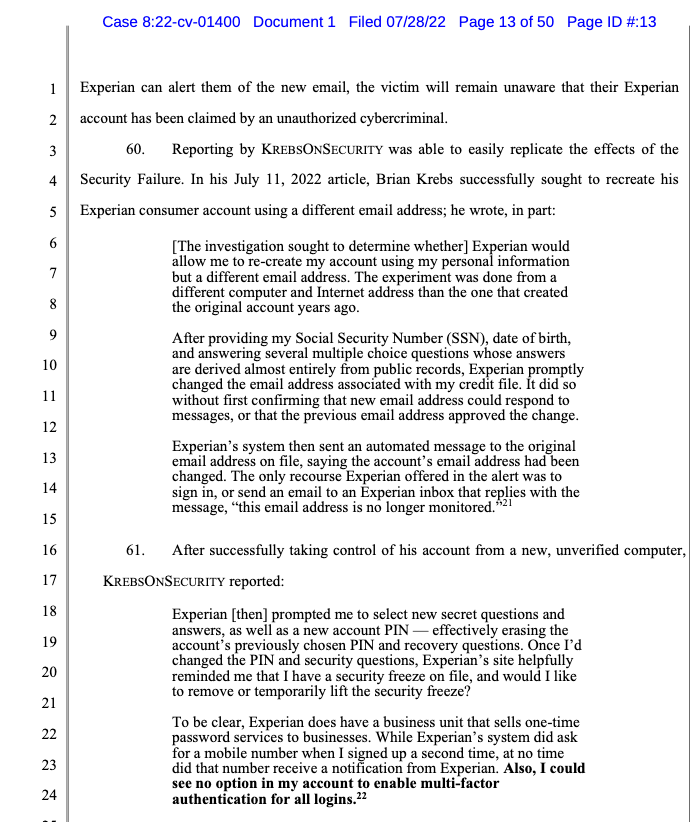
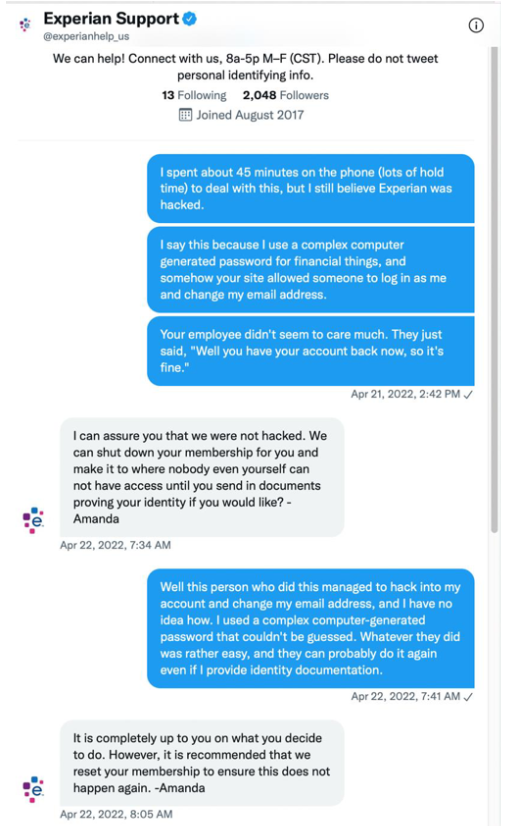


 The US is still lagging behind China in terms of vulnerability discovery and disclosure. While the gap between the US National Vulnerability Database (NVD) and the Chinese NVD (CNNVD) has slightly shrunk over the last 5 years, there are still hundreds of vulnerabilities registered in China that are yet to be listed on the US NVD. The CNNVD is a known subsidiary of the Chinese Ministry of State Security’s Technical Bureau, which drives Chinese cyber espionage, and has a history of altering CVE disclosure dates and providing APT groups with exploits.
The US is still lagging behind China in terms of vulnerability discovery and disclosure. While the gap between the US National Vulnerability Database (NVD) and the Chinese NVD (CNNVD) has slightly shrunk over the last 5 years, there are still hundreds of vulnerabilities registered in China that are yet to be listed on the US NVD. The CNNVD is a known subsidiary of the Chinese Ministry of State Security’s Technical Bureau, which drives Chinese cyber espionage, and has a history of altering CVE disclosure dates and providing APT groups with exploits.
 Vulnerabilities in System Management Mode (SMM) and more general UEFI applications/drivers (DXE) are receiving increased attention from security researchers. Over the last 12 months, the Binarly efiXplorer team disclosed 107 high-impact vulnerabilities related to SMM and DXE firmware components. But newer platforms have significantly increased the runtime mitigations in the UEFI firmware execution environment (including SMM). The new Intel platform firmware runtime mitigations reshaped the attack surface for SMM/DXE with new Intel Hardware Shield technologies applied below-the-OS.
Vulnerabilities in System Management Mode (SMM) and more general UEFI applications/drivers (DXE) are receiving increased attention from security researchers. Over the last 12 months, the Binarly efiXplorer team disclosed 107 high-impact vulnerabilities related to SMM and DXE firmware components. But newer platforms have significantly increased the runtime mitigations in the UEFI firmware execution environment (including SMM). The new Intel platform firmware runtime mitigations reshaped the attack surface for SMM/DXE with new Intel Hardware Shield technologies applied below-the-OS. Black Lotus Labs, the threat intelligence division within Lumen Technologies, is currently tracking elements of a sophisticated campaign that has been leveraging infected SOHO routers to target North American and European networks of interest undetected for nearly two years. We identified a multistage remote access trojan (RAT), dubbed ZuoRat, developed for SOHO devices that grants the actor the ability to pivot into the local network and gain access to additional systems on the LAN by hijacking network communications to maintain a foothold.
Black Lotus Labs, the threat intelligence division within Lumen Technologies, is currently tracking elements of a sophisticated campaign that has been leveraging infected SOHO routers to target North American and European networks of interest undetected for nearly two years. We identified a multistage remote access trojan (RAT), dubbed ZuoRat, developed for SOHO devices that grants the actor the ability to pivot into the local network and gain access to additional systems on the LAN by hijacking network communications to maintain a foothold. The proliferation of tooling such as ShadowPad across China-based APT actors and the existence of digital quartermasters has long been a feature of public reporting and a strong indication of ultimate actor sponsorship, based on US indictments and adjacent research.
The proliferation of tooling such as ShadowPad across China-based APT actors and the existence of digital quartermasters has long been a feature of public reporting and a strong indication of ultimate actor sponsorship, based on US indictments and adjacent research.