With summer on its last legs, the phrase “back to school” can be heard everywhere. For opportunistic threat actors though, this holds an entirely different meaning than it does for students, educators, and guardians. Data for 2022 in the US suggests that the education sector has seen an increase in monthly cyberattack volume since 2021. In the UK, government statistics indicate that 62% of higher education institutions reported experiencing breaches or attacks at least weekly in the previous 12 months.
On a global level, key statistics for 2022 showed that:
- In July, the education sector experienced double the number of weekly cyberattacks when compared to other industry averages.
- Education is the most targeted industry with an average of 2297 cyberattacks against organizations each week in the first half of 2022; a 44% increase compared to the first half of 2021.
Cybersecurity in K-12 and higher educational organizations is complicated by multiple factors, including a large and disparate attack surface, varying degrees of cybersecurity awareness among users, restricted budgets, and the need for strategic oversight at the management level. On top of that, schools sit on a honeypot of valuable personal data belonging to students, staff and even parents that is attractive to threat actors.
In this post, we review the risks facing the education sector and discuss recent policy initiatives and cyber defense solutions to help schools, colleges, and universities better manage the cybersecurity challenges they face.

Student PII and Education Software
As school districts lean further into digitizing their methods of teaching, learning, and managing students’ progress, threat actors are leveraging these tools as springboards to accessing student data. In particular, student tracking software is a direct gateway for actors to obtain students’ personally identifiable information (PII), defined by NIST as any data that can be used to distinguish or trace an individual’s identity.
Student tracking software is used by educators to document and manage day-to-day student data such as absenteeism, learning or developmental challenges, disciplinary action plans, reporting, and more. While this type of software greatly helps educators support students, threat actors are targeting the technology for malicious purposes.
The data breach reported by California-based education technology (ed-tech) vendor, Illuminate Education, is a recent example of this. Illuminate Education, which integrates K-12 technology systems for student instruction, assessment, and data analytics fell victim to a data breach, exposing student PII across two of the US’ largest public school systems, New York City Department of Education and Los Angeles Unified School District (LAUSD) with cyber incidents beginning to crop up in other states as well. This breach is especially concerning as Illuminate Education claims to reach 17 million students across 5200 American school districts.
Cybercriminals Hone in on School Data Stockpiles
Schools and the technology they use to collect and manage information offer an attractive target for threat actors as they represent a gateway to data, and lots of it. Schools hold large amounts of sensitive data not only on their students but also on parents and staff.
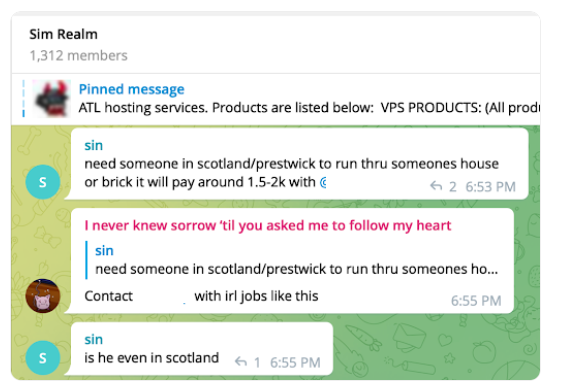
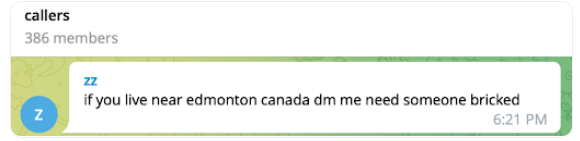
Unfortunately, where there is data online, there is cyber risk. Sensitive data such as addresses, birthdays, social security numbers, loan applications, and tuition-related banking information can all be targeted by threat actors, who advertise it for sale on online criminal marketplaces and publicly-accessible forums. Even delicate data like notes about a student’s home life, illnesses, ethnicity, test scores, citizenship or migration status can be leveraged by threat actors in reconnaissance efforts and profiling.
In the short term, the consequences of exposing PII stored by the school could lead to a variety of cyberattacks including data breaches through phishing, ransomware attacks, Distributed-Denial-of-Service (DDoS) attacks, and even hacktivism through “zoom-bombing”, “meeting invasions”, and email spamming.
Identity theft is another cyber risk stemming from compromised student PII. Higher education institutions are particularly likely to report impersonation attacks. However, the problem has also been reported in K-12 schools as well. Earlier this year, one family found that their child’s name was being used to apply for a credit card, car loan, and discounts on their “child’s” electric utility account. The child’s personal information had been part of a data breach at their elementary school just a few months prior. From a threat actor’s perspective, credit checks are rarely conducted on children and teenagers, meaning any fraudulent activity carried out in their names may not be noticed until months and years later.
In terms of long-term consequences, there is the potential for stolen PII to be misused in ways that could affect a future college, loan, or even job application. In the Illuminate Education data breach, reports stated that personal details of both present and former students dating back more than a decade had been compromised.
Attention & Action Taken at the Federal Level
Mounting cyberattacks on education are making their way to policymakers at the federal level. In late 2021, President Biden signed the K-12 Cybersecurity Act calling for the Cybersecurity and Infrastructure Security Agency (CISA) to analyze cyber risks faced by elementary and secondary schools and develop recommendations on how to assist them in facing threats.
In March of this year, President Biden’s State of the Union address called on Congress directly to strengthen privacy protections for children, including the collection of their personal data.
This was followed in June 2022 by the Federal Trade Commission (FTC) issuing a policy statement reiterating the Children’s Online Privacy Protection Act (COPPA) for ed-tech providers. Their August statement outlined the following:
- Providers must not collect more information than is necessary when accessing a child’s online activity,
- A child’s personal personal information can only be used for the benefit of their school,
- A child’s personal personal information cannot be kept longer than needed for the specific purpose of data collection, and
- Processes must be put in place to maintain the privacy, security, and integrity of the child’s personal information.
#StopRansomware | Vice Society
In their latest joint cybersecurity advisory, CISA, the FBI, and the Multi-State Information Sharing and Analysis Center (MS-ISAC) reported on increasing ransomware attacks on the education sector by intrusion, exfiltration, and extortion hacking group, Vice Society.
US authorities warn that “Vice Society actors [are] disproportionately targeting the education sector with ransomware attacks.” The group is known to deploy common ransomware available on the darknet such as HelloKitty and Zeppelin.
Outlining the scope of impact to include “restricted access to networks and data, delayed exams, canceled school days, and unauthorized access to and theft of personal information regarding students and staff”, attacks by this particular hacking group is just one example amongst the wave of attacks on the sector.
As the school year starts this week across American schools, the FBI, CISA, and MS-ISAC anticipate the number of attacks to increase. At a higher level, this joint advisory is part of an ongoing #StopRansomware effort published to detail observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IoCs) to help network defenders and organizations protect against ransomware.
SentinelOne in Defense of the Education Sector
While more restrictive policies are yet to be enforced on ed-tech vendors, vulnerable school districts are not helpless against cyberattacks. Schools can bolster their cyber defenses against ransomware, DDoS attacks, identify theft, and more by implementing a single, robust security platform to ensure full transparency across their networks and endpoints.
Many schools without the resources to fund and staff dedicated security teams choose to outsource cybersecurity to an MSP (Managed Service Provider) or MSSP (Managed Security Service Provider), an increasing number of which rely on SentinelOne’s Singularity platform to provide managed security services to schools and other organizations.
Educational institutions can partner directly with SentinelOne and take advantage of AI-powered prevention, detection, response, and advanced threat hunting capabilities. SentinelOne’s single autonomous platform delivers protection for Chromebooks, Macs, Windows and Linux devices, as well as server and cloud workload protection. The school’s IT team can see everything happening across their network at machine-speed, staying ahead of threat actors and preventing malicious behavior from developing into full-blown cyberattacks. Schools, colleges, and universities can also rely on SentinelOne’s integrated Identity solution to help prevent breaches through the abuse or theft of credentials.
Conclusion
Protecting the data, services and users within educational organizations is a challenge that requires a coordinated strategy. The complexity of the threat along with the squeeze on resources means planners need to be aware of the risks they face and current government guidelines. Partnering with external cybersecurity providers and deploying a modern, trusted security solution can help address these challenges within the school’s budget.
Leveraging our deep industry knowledge and experience with fighting back privileged escalation and lateral movement, SentinelOne’s Singularity XDR delivers comprehensive security with autonomous protection. Through AI-based behavioral detection and superior detection of ransomware attacks, SentinelOne eases the burden on under-resourced school IT teams, leaving staff to focus their attention on operational tasks instead.
XDR delivers comprehensive security with autonomous protection. Through AI-based behavioral detection and superior detection of ransomware attacks, SentinelOne eases the burden on under-resourced school IT teams, leaving staff to focus their attention on operational tasks instead.
To learn more about how SentinelOne helps protect K-12 and higher education, please contact us or request a demo.
Singularity for ChromeOS
Real-Time Protection for Chromebooks



 XDR
XDR